Connect testing, detection, and response into one continuous workflow.
Security teams aren’t lacking tools. They’re lacking alignment.
Offensive testing, defensive monitoring, and compliance efforts all operate in parallel, using different systems, producing different data, and following different workflows. Each function provides value on its own, but together they create fragmentation.

Security data is spread across scanners, SIEMs, cloud platforms, and ticketing systems. Without a unified view, teams struggle to understand where real risk exists at any given moment.
Vulnerabilities are identified, alerts are triggered, reports are generated, but remediation is inconsistent. Without clear prioritization and ownership, critical issues remain unresolved longer than they should.
Teams measure success by outputs like scans completed, alerts triaged, and audits passed. But these activities don’t guarantee that risk is actually being reduced.
With data fragmented across tools and teams, leadership is left reconciling reports instead of making decisions. The question remains difficult to answer: Where are we actually at risk right now?
Security teams don’t need more tools, they need a better way to operate.
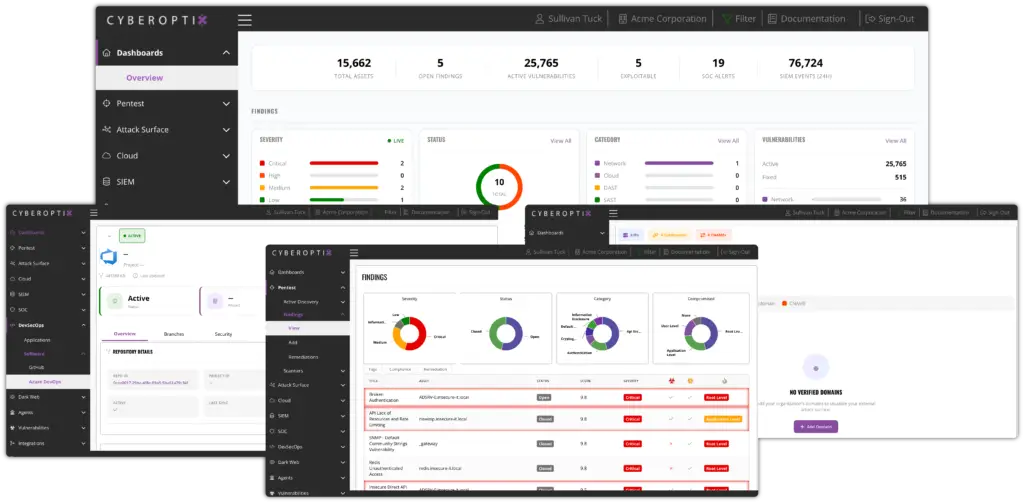
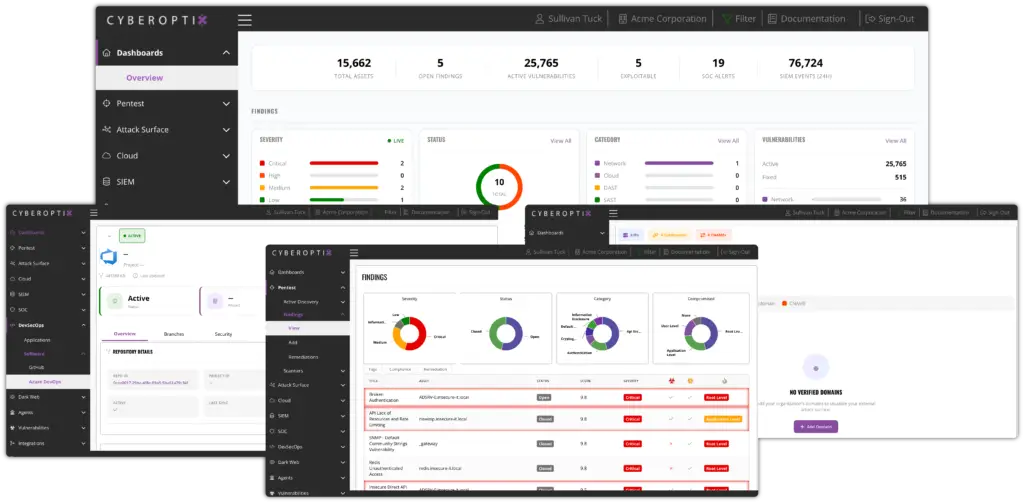
CyberOptix is built on the principle of purple teaming, unifying offensive testing and defensive operations into a single, continuous workflow. By connecting how risk is identified, validated, and remediated, it enables security to function as an ongoing process rather than a series of isolated activities.
This operational model is what makes continuous exposure management possible.

Continuously identify exposures across your environment using offensive testing, telemetry, and external intelligence.
Correlate findings and detection data to confirm real, exploitable risk and eliminate noise.
Route validated issues to the right teams with context, ownership, and tracking to ensure remediation is completed.
CyberOptix was built and refined over seven years within TrollEye Security, supporting continuous testing, validation, and remediation across real-world environments.
Through this operational model, organizations have been able to eliminate critical and high-risk findings, achieve up to a 97%+ reduction in overall vulnerabilities, and maintain consistent progress in reducing exposure over time.
CyberOptix unifies application, cloud, network, endpoint, vulnerability management, threat intelligence, security operations, and compliance into a single operational platform.
AI-assisted analysis correlates data across these domains to validate real risk, prioritize what matters, and accelerate remediation, helping teams focus on action instead of noise.