Security operations weren’t designed to be fragmented, but that’s what they’ve become.
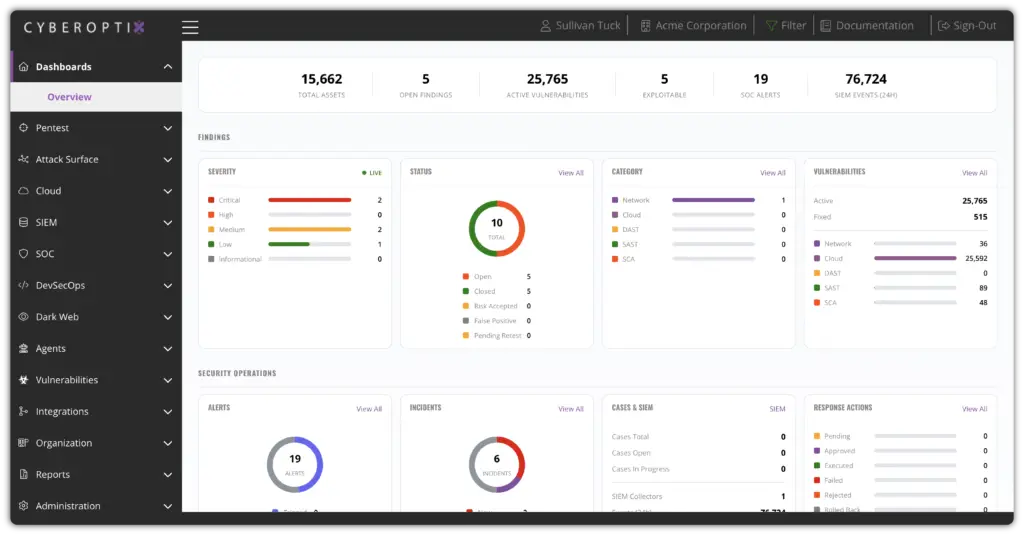
CyberOptix is designed to do more than surface risk. It transforms how security teams operate by turning fragmented data, tools, and processes into a unified, continuous system. The result is measurable outcomes that improve visibility, accelerate remediation, and simplify compliance.
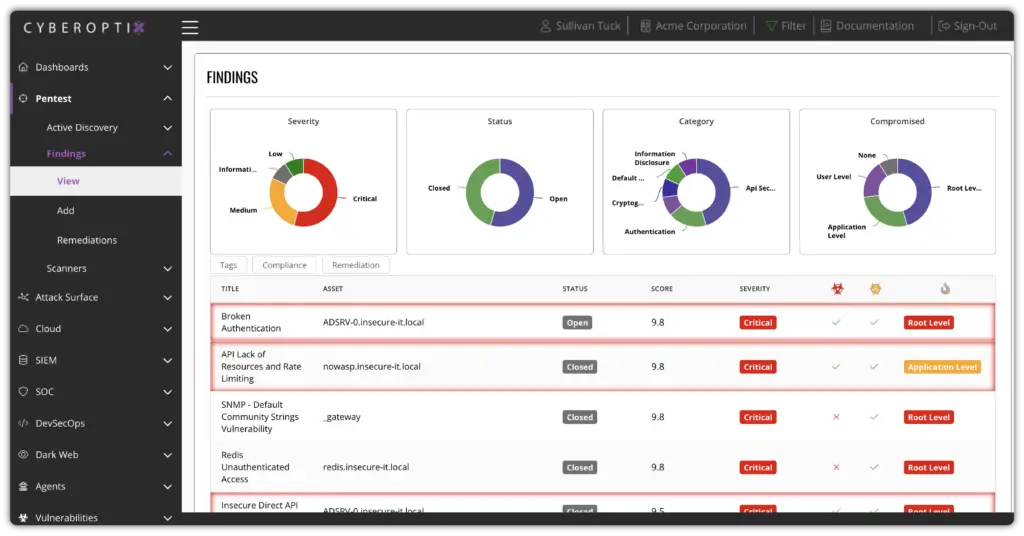
Replace delayed reporting cycles with a continuous, accurate view of your security posture.
CyberOptix eliminates static reports and fragmented data by delivering real-time exposure insights across your environment. Security leaders gain immediate visibility into what matters most, which risks are exploitable, and how remediation is progressing without waiting for the next assessment cycle.
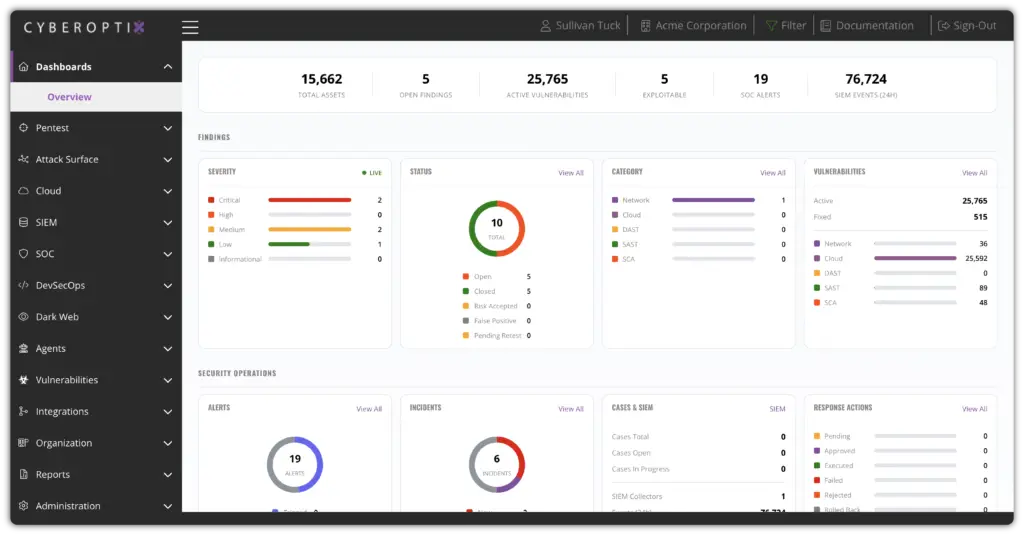
Move from identifying issues to resolving them with speed and accountability.
CyberOptix connects offensive testing, detection data, and remediation workflows into one operational system. Findings are automatically routed to the teams responsible for fixing them, with full context on exploitability and business impact.
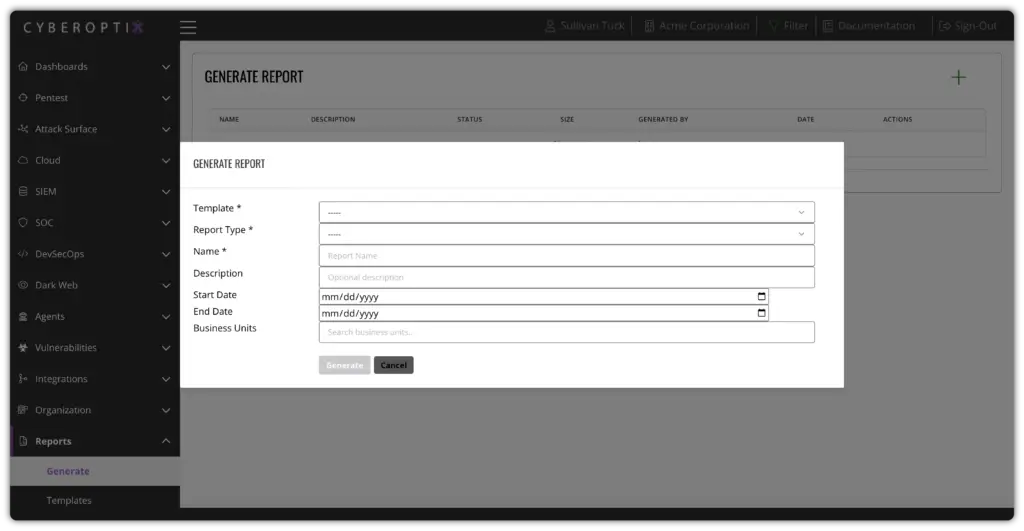
Stay audit-ready at all times without the overhead of manual evidence collection.
CyberOptix maps security activity directly to compliance requirements, automatically generating and maintaining the documentation needed for audits. Instead of scrambling to prepare for assessments, organizations maintain a continuously updated, defensible record of their security posture.

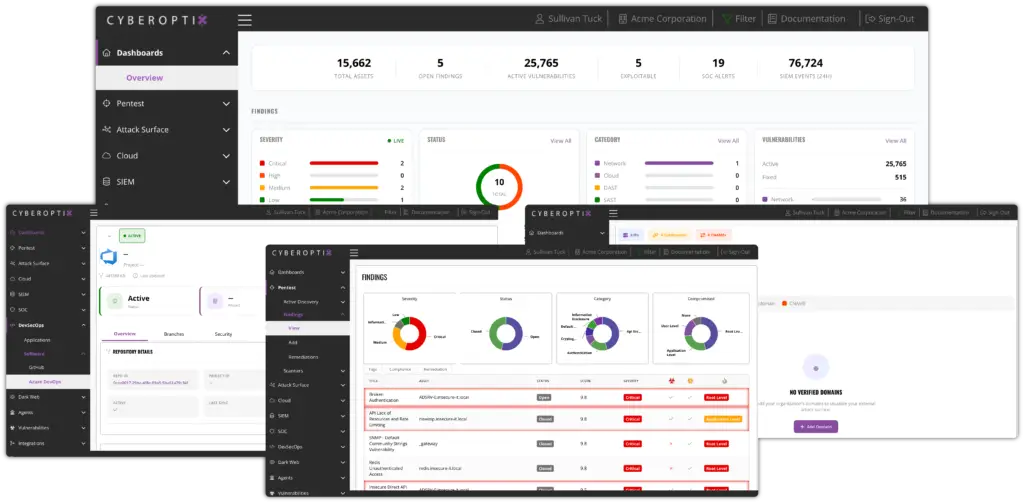
CyberOptix combines native security capabilities with integrations across developer tools, cloud platforms, and security infrastructure to provide a unified operational view of risk. Integrates with your existing Cloud, EDR, Code Management, Firewalls, Ticketing, and Communication tools.

Continuously identify and validate application-layer risk within your development pipelines, ensuring vulnerabilities are caught and addressed before release.

Monitor your external attack surface and the dark web to identify exposed assets, leaked data, and emerging threats before they can be exploited.

Continuously identify and validate application-layer risk within your development pipelines, ensuring vulnerabilities are caught and addressed before release.

Gain unified visibility into cloud environments to detect misconfigurations, exposed services, and security gaps across infrastructure.

Correlate network data to uncover exploitable paths, lateral movement opportunities, and weaknesses attackers can leverage.

Unify detection and response data to validate threats, reduce noise, and ensure security teams focus on what is actually actionable.

Leverage endpoint telemetry to identify active threats in context, connecting device-level activity to broader exposure and risk.

Gain unified visibility into cloud environments to detect misconfigurations, exposed services, and security gaps across infrastructure.
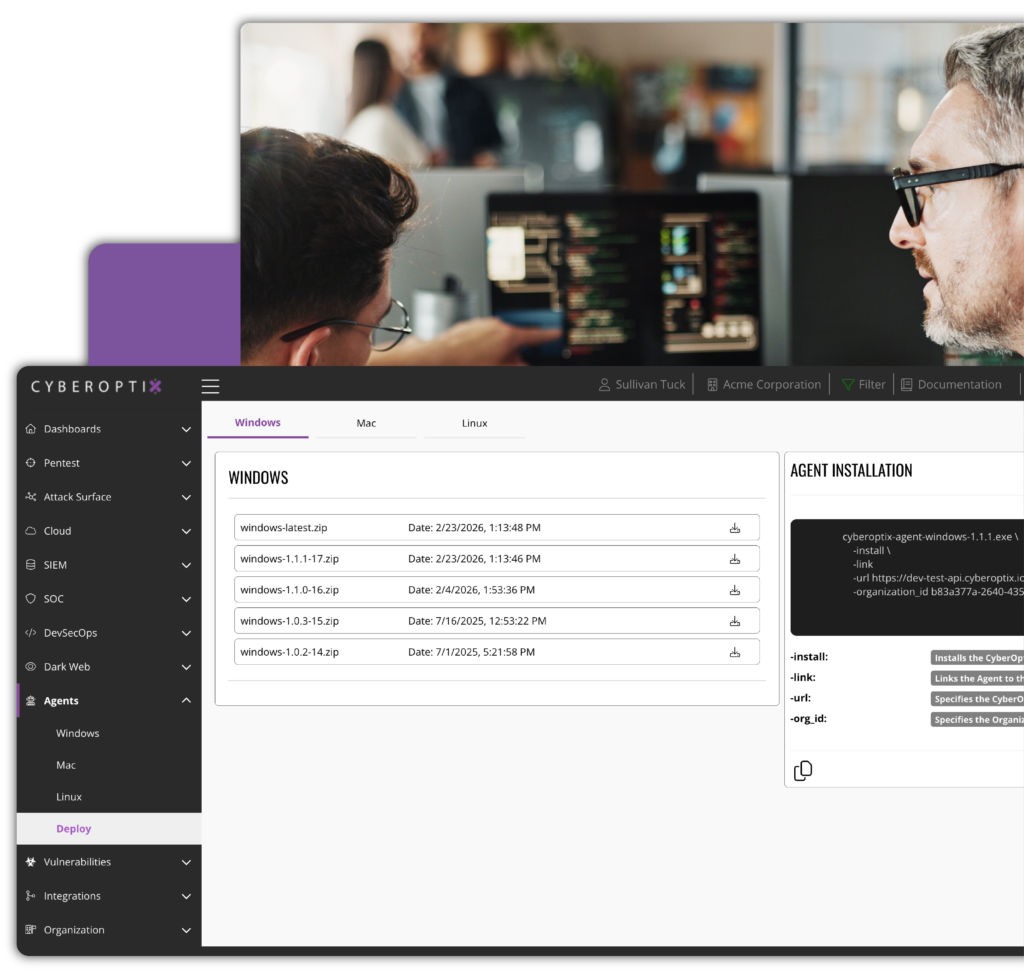
CyberOptix applies AI-assisted analysis across offensive and defensive data to help security teams cut through noise, validate real threats, and act faster. These agents don’t replace analysts, they enhance decision-making by connecting fragmented data into clear, actionable insights.


Correlates detection data with real-world exposure to validate alerts and reduce noise. By connecting telemetry with actual risk, it helps security teams focus on threats that matter, not just alerts that trigger.

Analyzes validated findings to prioritize exploitable vulnerabilities and surface real attack paths. This ensures teams focus remediation efforts on what an attacker could actually use.

Enriches scanner-generated findings with threat intelligence and context, improving prioritization and helping teams quickly identify which vulnerabilities require immediate action.
CyberOptix is designed to unify your security operations, not replace everything you already rely on. It integrates directly with the tools your teams use every day, cloud platforms like AWS, development environments like GitHub and Azure DevOps, security tooling like CrowdStrike and Palo Alto, and core infrastructure across your environment, bringing all of that data into one continuous exposure management workflow.
Instead of forcing teams to swivel between disconnected systems, CyberOptix centralizes visibility while pushing validated findings back into your existing processes. Issues are routed directly into tools like Jira or ServiceNow, enriched with context, and assigned to the right owners so remediation actually happens.


Leverages endpoint telemetry to enrich findings and validate real-world exploitability, helping prioritize threats based on actual attacker behavior.
Incorporates firewall and network security data to identify misconfigurations and validate exploitable paths across your network layer.

Pushes validated findings directly into Jira with clear ownership and context, turning security issues into actionable tasks within existing development workflows.

Continuously monitors cloud infrastructure for misconfigurations and exposure risk, validating findings so your team can secure what actually matters in your AWS environment.

Ingests network and firewall data to uncover and validate perimeter exposures, improving visibility into how attackers could move through your environment.

Integrates with repositories to support secure development practices, enabling continuous testing and validation throughout the SDLC without slowing releases.

Extends visibility into GCP environments to identify and validate cloud exposures, ensuring consistent security across multi-cloud infrastructure.

Enriches and validates exposures with endpoint telemetry to prioritize real, active threats.
CyberOptix is a Purple Teaming Platform that unifies security operations so offensive testing, defensive telemetry, and remediation workflows operate as a continuous process rather than isolated engagements. Schedule a walkthrough with our team to see it live.