Helping security teams find, prioritize, and remediate critical vulnerabilities before attackers can exploit them.
Most organizations are drowning in vulnerability data. Scanners generate thousands of findings, but without context, prioritization, or clear ownership, security teams spend more time managing spreadsheets than closing real exposures.
CyberOptix’s Vulnerability Management solution is designed to change that.
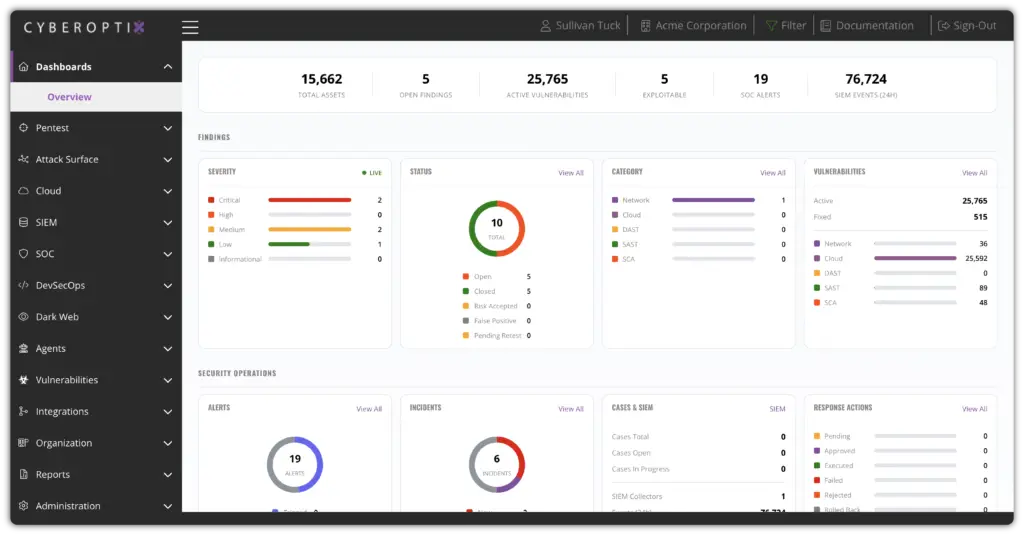
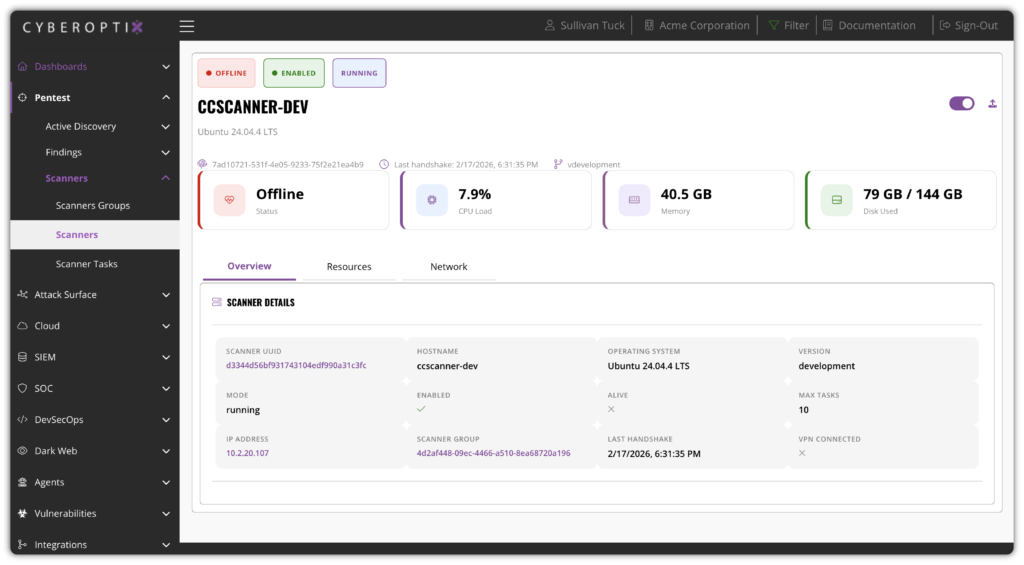
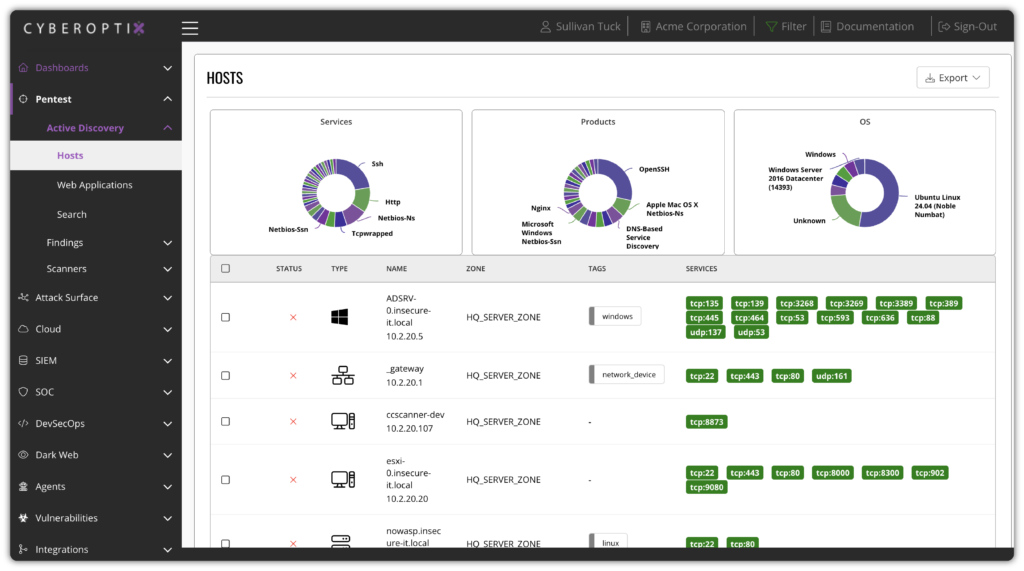
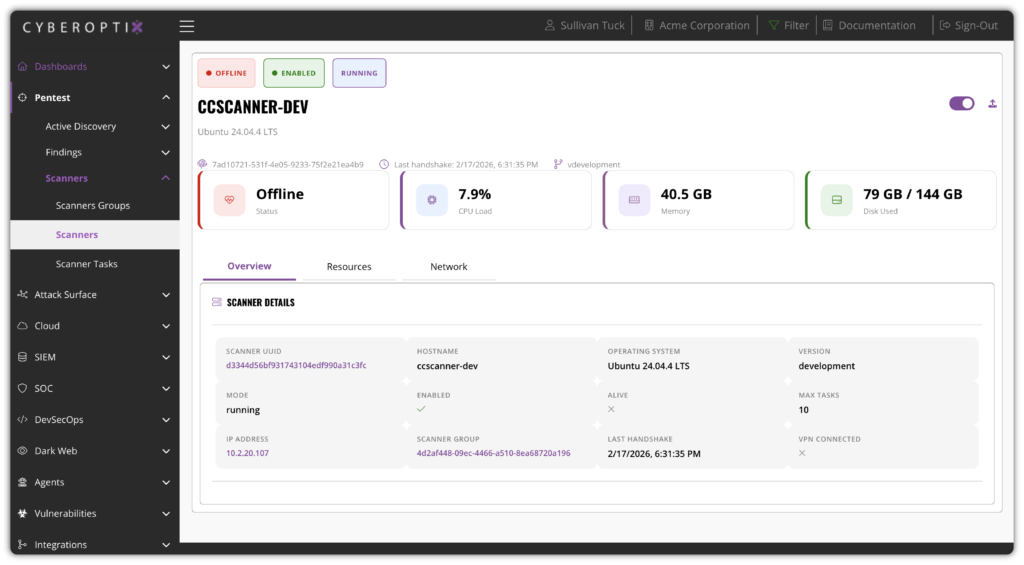
Vulnerabilities are identified continuously across your entire environment—infrastructure, endpoints, applications, and cloud—and tracked from discovery through to verified remediation.
Instead of point-in-time scans that go stale overnight, CyberOptix delivers an always-current view of your vulnerability exposure so your team can act on what matters most.
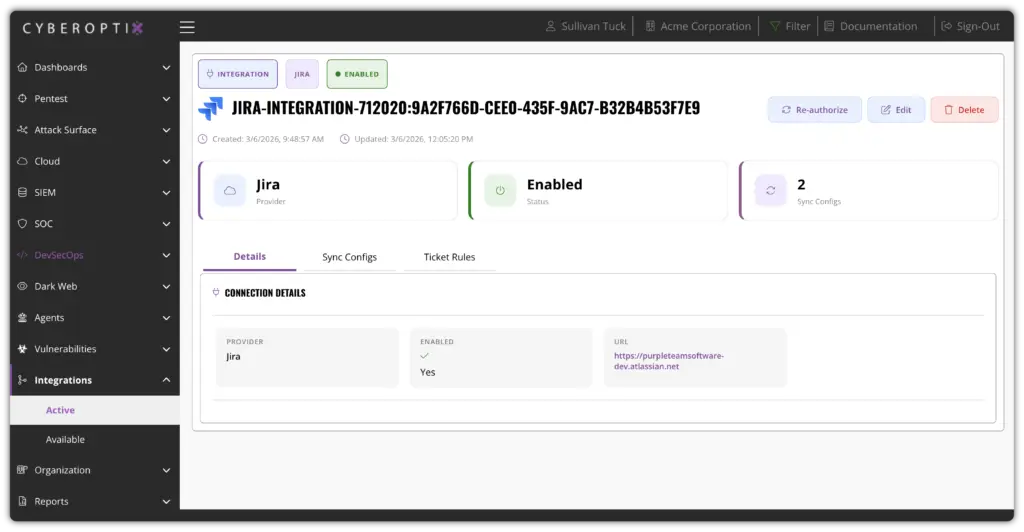
Vulnerability data integrates directly with the tools and workflows your teams already use—ticketing systems, SIEM platforms, and asset management tools—delivering prioritized findings with clear remediation ownership and context.
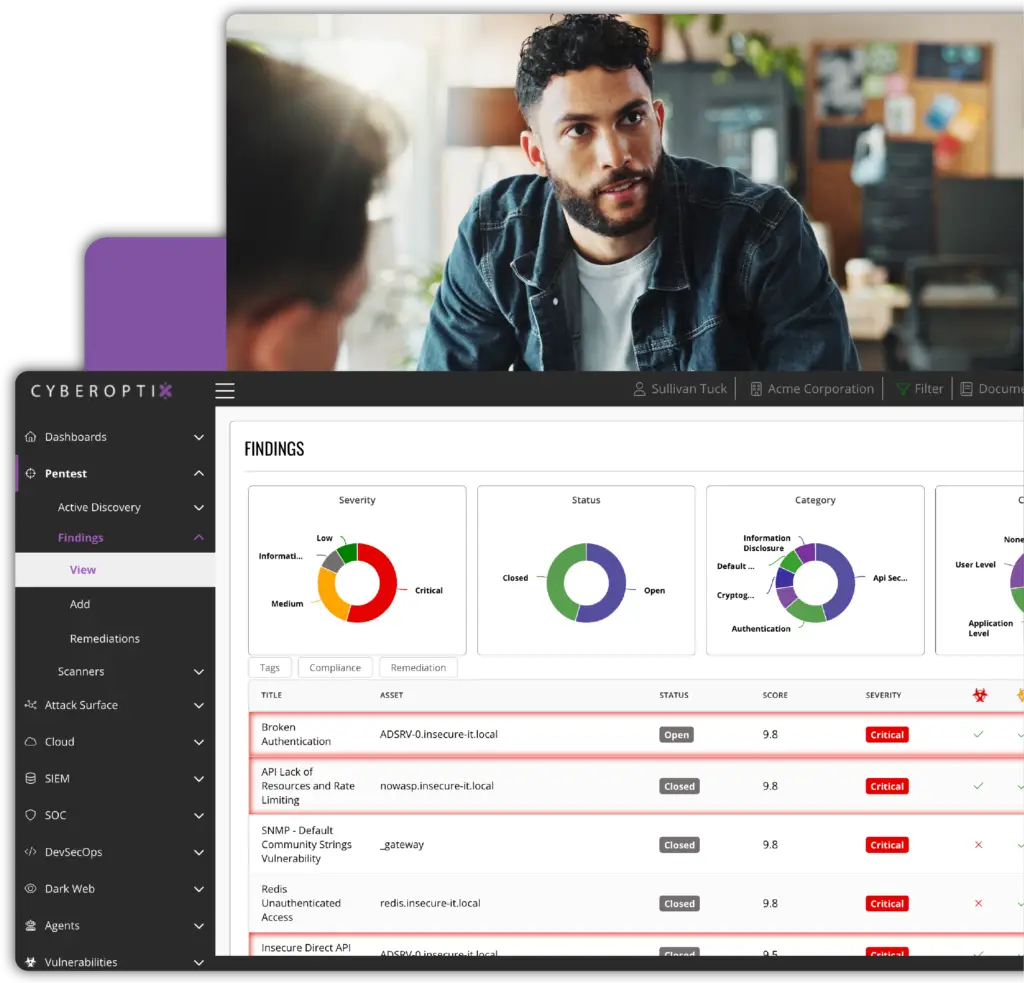
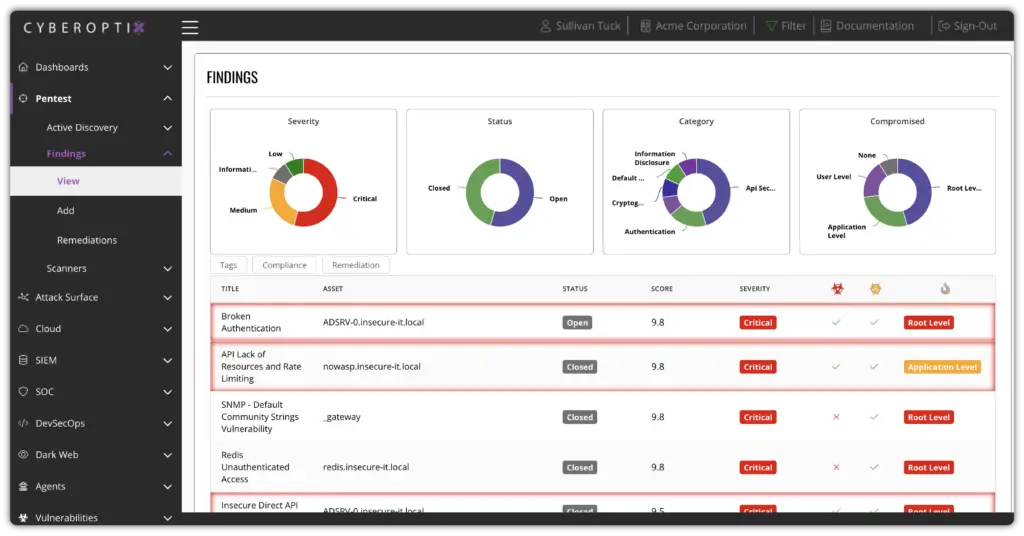
Findings are tied to real assets, real risk scores, and real remediation paths so teams can close vulnerabilities faster without drowning in noise.
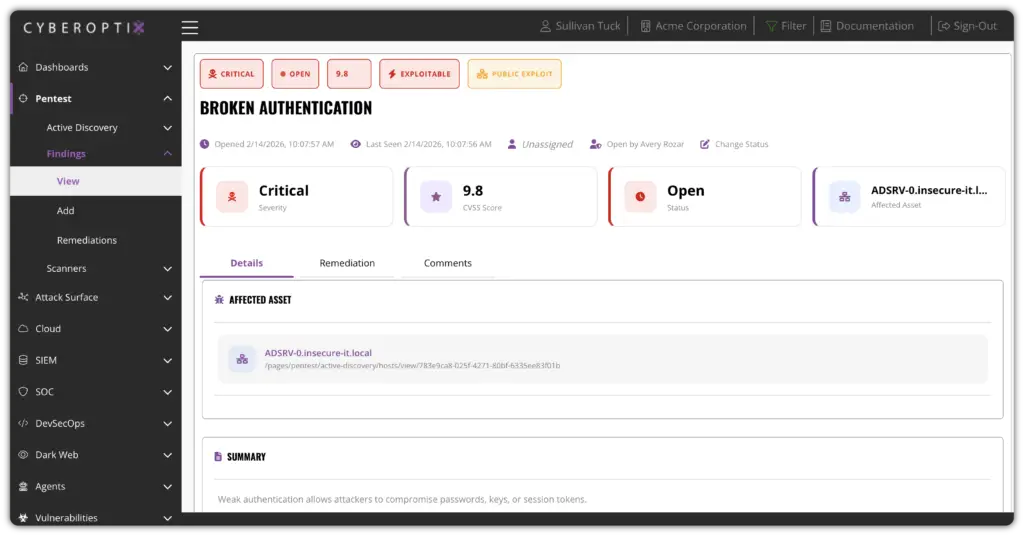
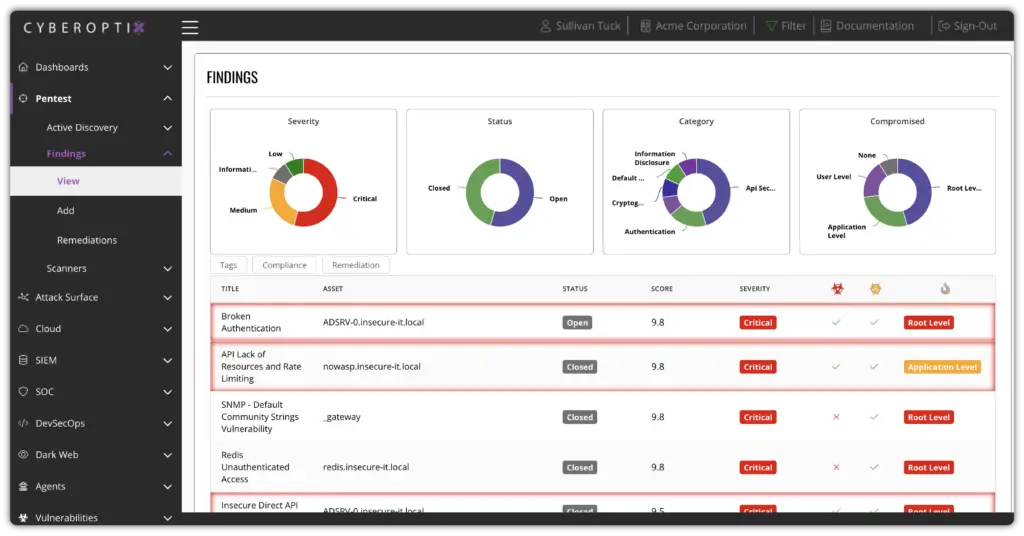
Vulnerabilities are validated for real-world exploitability, assigned severity scores based on asset criticality and threat context, and tracked against remediation SLAs with clear ownership.
Instead of overwhelming teams with static reports, vulnerability risk is prioritized based on exploitability and business impact. The right issues are escalated to the right owners—reducing mean time to remediate and preventing recurring exposure.
Vulnerability management matures over time as CyberOptix tracks remediation trends, recurring exposures, and risk reduction progress across your environment.
Security posture improves continuously, not just at audit moments. Executive-ready reporting, compliance mappings, and trend dashboards give leadership the visibility they need to validate program effectiveness.
CyberOptix delivers vulnerability management as an ongoing operational capability, not a compliance checkbox. These core capabilities work together to continuously identify exploitable risk, prioritize what matters, and help teams remediate vulnerabilities as part of their everyday workflow.

Continuously scan on-premises systems, cloud workloads, containers, and web applications to identify known vulnerabilities (CVEs), misconfigurations, and exploitable weaknesses. Centralize all findings into a single, prioritized view.
Go beyond CVSS scores. CyberOptix correlates vulnerability data with threat intelligence, asset criticality, and active exploit activity to surface the vulnerabilities that pose the greatest real-world risk—so teams focus remediation effort where it matters.
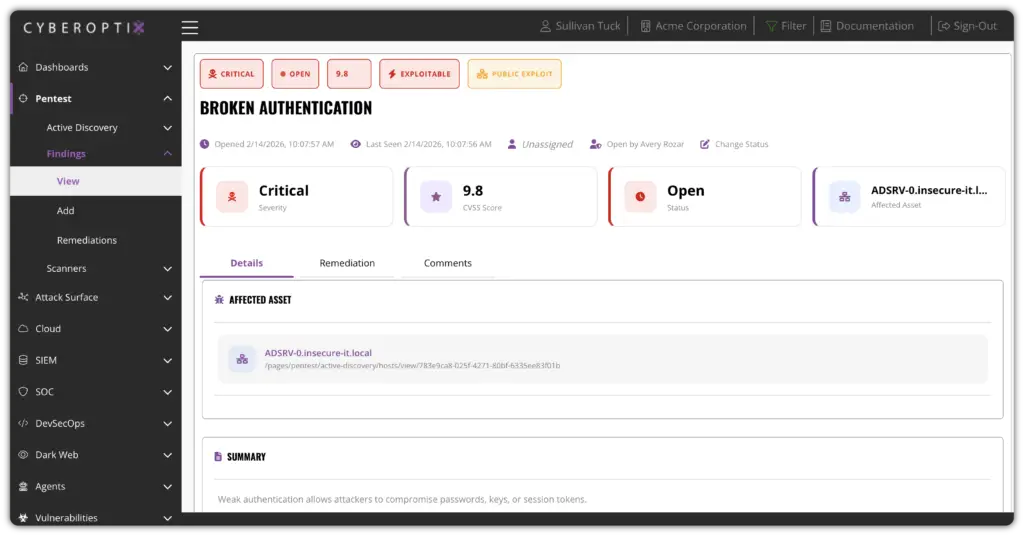
Assign remediation ownership, set SLA targets by severity, and track progress from initial discovery to verified closure. Automated workflows ensure the right team members are notified and accountable, reducing mean time to remediate.
Connect vulnerability findings to your existing security stack—SIEM platforms, ITSM tools, and threat intelligence feeds—so vulnerability data flows seamlessly into the workflows your team already uses for response and remediation.
CyberOptix transforms vulnerability management from a periodic scan exercise into a continuous, risk-driven program. See how unified discovery, intelligent prioritization, and end-to-end lifecycle tracking work together to reduce your real exposure—not just your finding count.