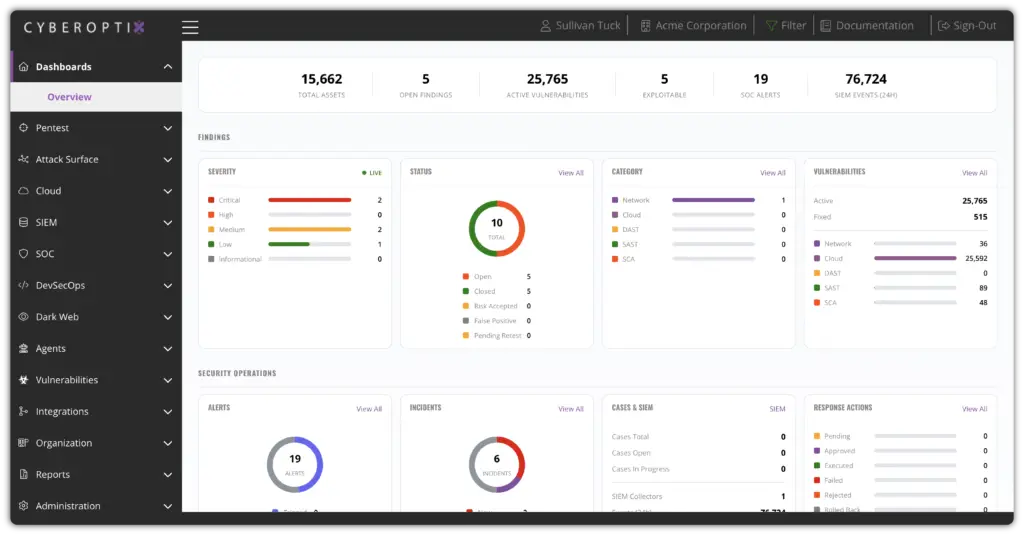
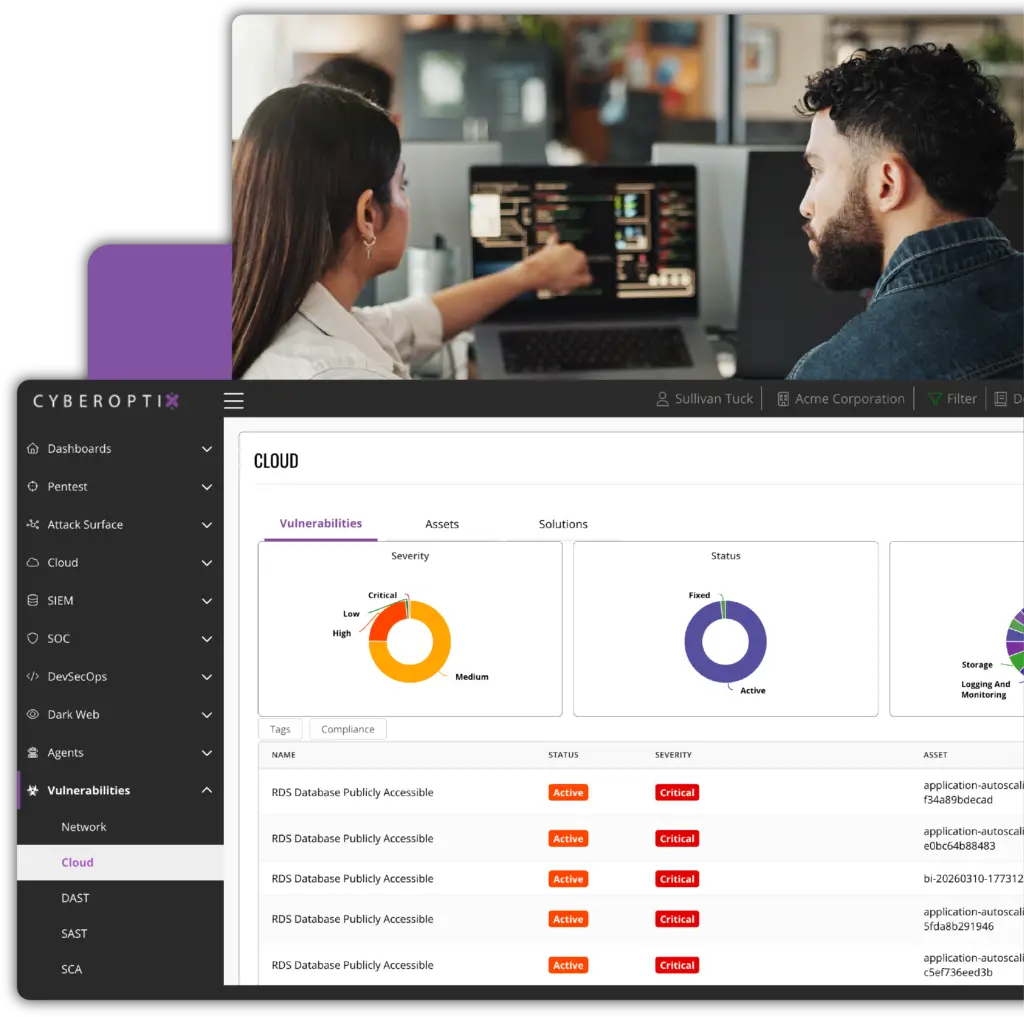
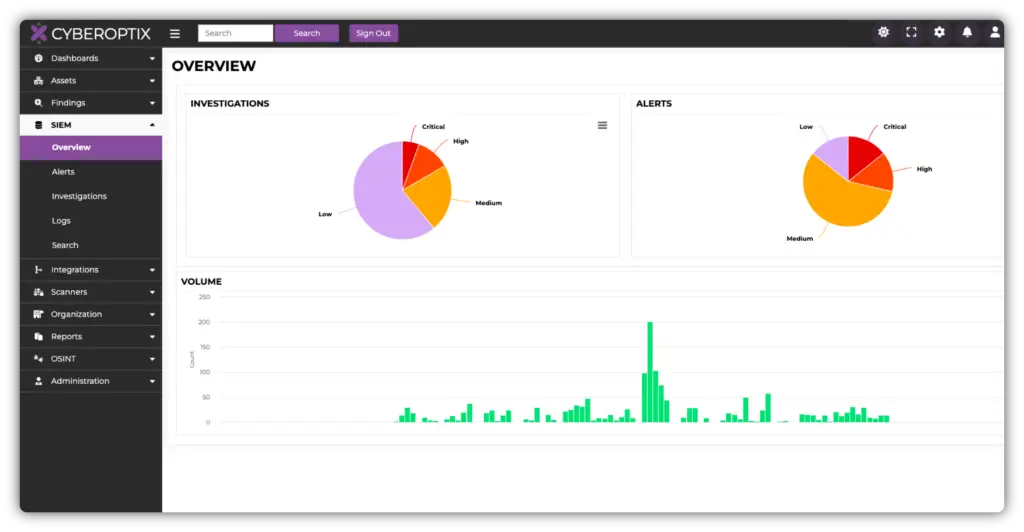
Misconfigurations are the leading cause of cloud breaches. CyberOptix continuously scans your cloud environment—AWS, Azure, GCP—identifying insecure storage buckets, overly permissive IAM roles, open ports, and hundreds of other risky settings before attackers find them first.
Cloud security posture is monitored in real time, not on a scan schedule. Every new resource is evaluated on deployment, so drift is caught immediately and your attack surface stays under control.
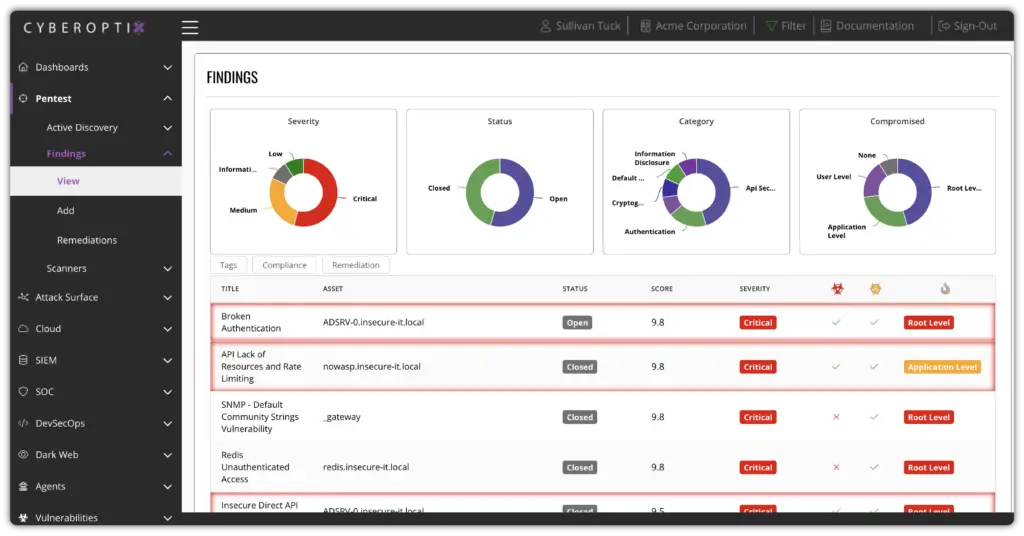
Security testing is built directly into the development lifecycle, identifying and validating exploitable vulnerabilities as code changes—before they ever reach production.
Application security becomes part of the development lifecycle instead of a final checkpoint. Vulnerabilities are identified early, validated in context, and addressed before they can be exploited in the wild.
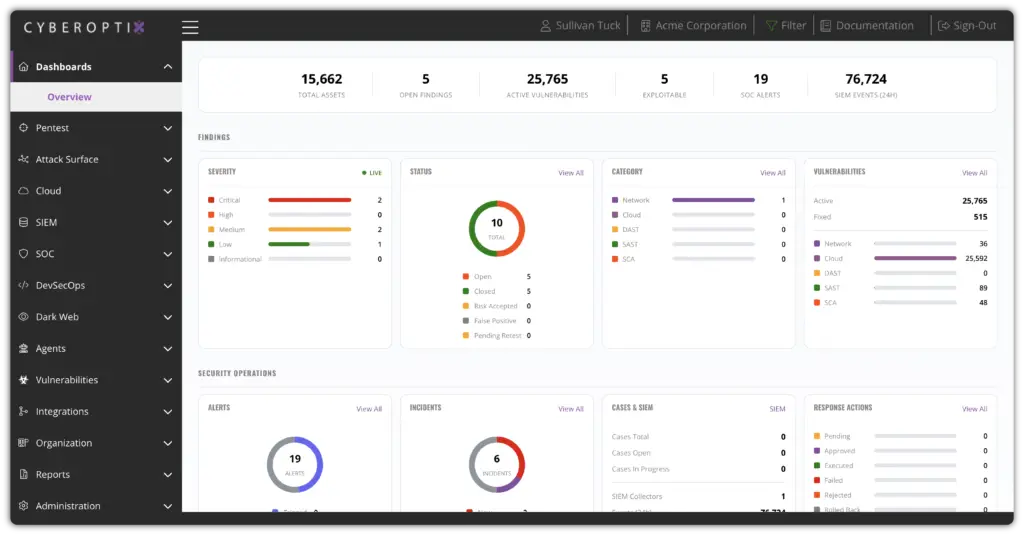
Not all cloud security findings are equally urgent. CyberOptix correlates misconfigurations, vulnerabilities, and exposures with real-world exploitability and business context—so your team knows exactly which issues to fix first and why.
Instead of drowning in alerts, security teams see a clear, ranked view of cloud risk. The highest-impact issues are surfaced to the right owners with the context needed to act, reducing mean time to remediation across the entire cloud environment.
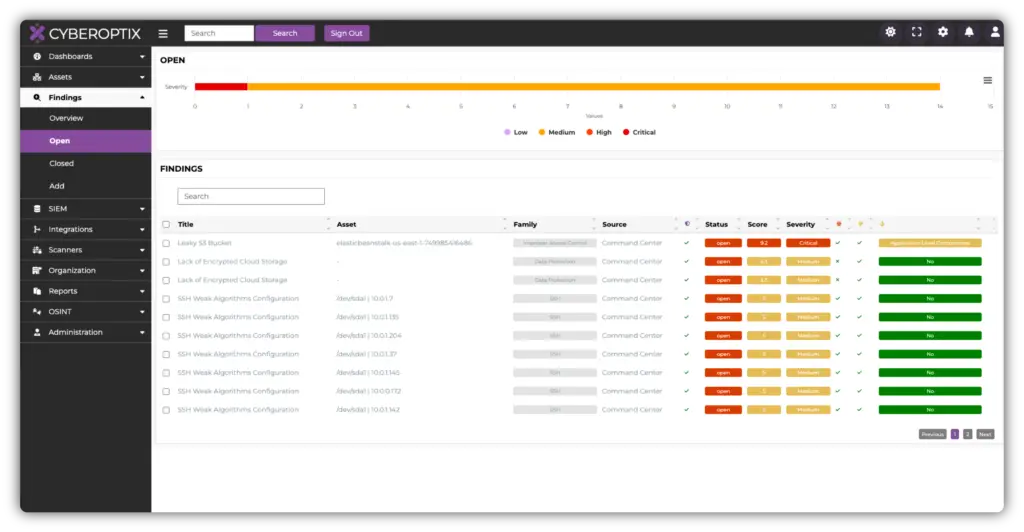
Vulnerabilities are validated for real-world exploitability, prioritized by impact, and routed to the right teams with clear ownership and remediation context.
Instead of overwhelming teams with static reports, application risk is prioritized based on exploitability and impact. The right issues are surfaced to the right owners, accelerating remediation and preventing repeat issues.
Each release benefits from the same consistent testing and validation process, reducing security drift and improving application security maturity over time.
Security posture improves over time, not just at audit moments. Each release benefits from the same level of testing, validation, and visibility, reducing drift and eliminating “surprise” vulnerabilities late in the process.
CyberOptix delivers application security as an operational capability, not a point-in-time exercise. These core capabilities work together to continuously identify exploitable risk, prioritize what matters, and help teams remediate issues as part of everyday development.

Identify insecure coding patterns and vulnerabilities directly within source code as it is written and updated. This enables teams to catch issues early, when fixes are faster, less disruptive, and more cost-effective.
Test running applications to uncover vulnerabilities that only appear during execution and user interaction. This provides visibility into exploitable flaws that static analysis alone cannot detect.
Identify vulnerable open-source libraries and third-party components embedded within applications. This helps teams reduce supply chain risk and address inherited vulnerabilities that often go unnoticed.
Integrate application security testing into pipelines and repositories so checks run automatically during builds, merges, and releases. This keeps security aligned with developer workflows without adding manual steps.
CyberOptix turns application security from a periodic task into a repeatable capability built into how software is delivered. See how continuous testing, workflow integration, and centralized risk management work together to reduce real application risk without slowing development.