Network Security Solution
Enabling security teams to detect, contain, and respond to network threats before they disrupt operations or reach critical assets.
Network Security That Keeps Threats Out and Operations Running
Modern network threats don’t come from a lack of tools. They come from fragmented visibility, inconsistent policy enforcement, and security teams that can’t distinguish real threats from background noise in time to act.
CyberOptix’s Network Security solution is designed to change that.
Continuous Network Monitoring and Threat Detection
Network activity is monitored continuously across every segment, device, and connection—identifying anomalies and threat indicators in real time, before damage is done.
Network security becomes an operational discipline, not a reactive fire drill. Threats are detected as they emerge, correlated across data sources, and escalated to the right teams with the context they need to act.
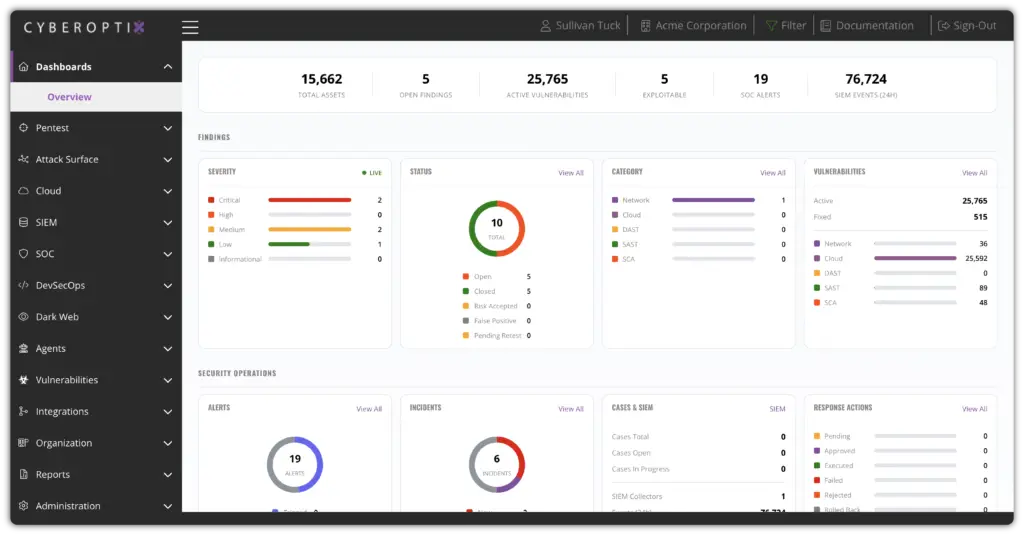
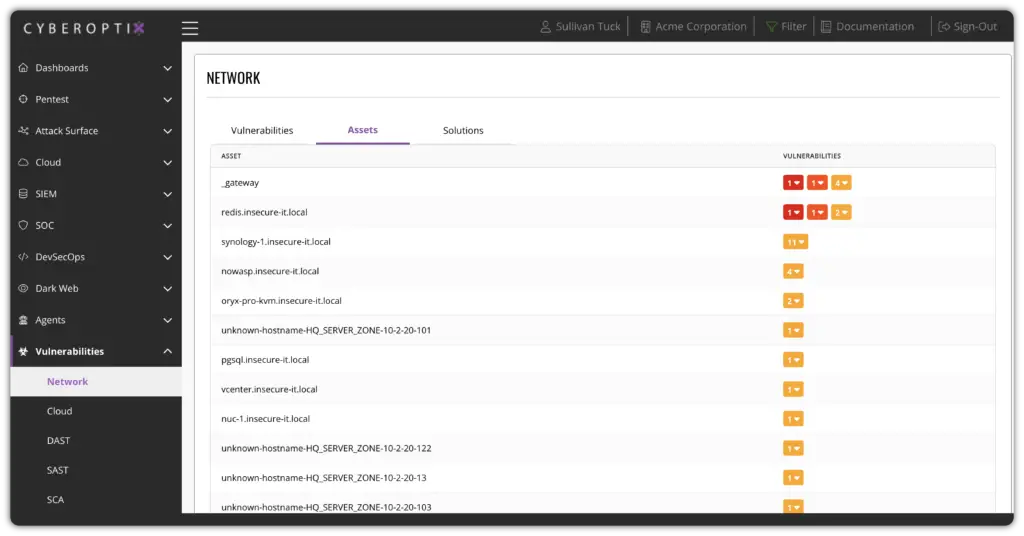
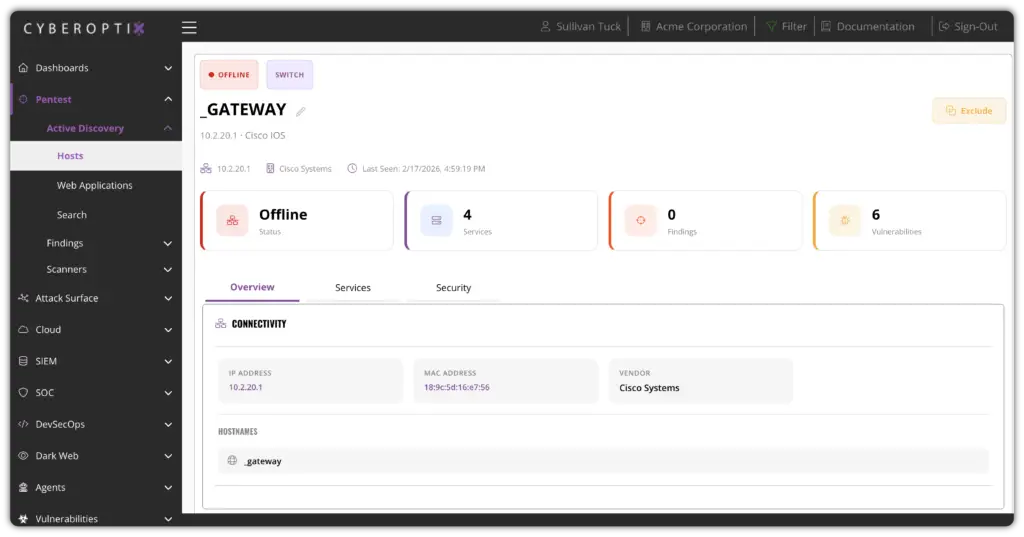
Unified Visibility Across Your Entire Network
Every device, connection, and user session is visible from a single pane of glass—giving security teams the context they need to spot lateral movement, unauthorized access, and policy violations.
Instead of managing security piecemeal across tools and silos, network risk is tracked holistically. The right alerts reach the right teams, accelerating response and preventing incidents from escalating.
Security Controls That Align With How Your Network Operates
Security controls are applied consistently across the network—mapping to how traffic actually flows and how teams actually operate—without creating bottlenecks or gaps in coverage.
Network security integrates with existing infrastructure and workflows, not against them. Policies are enforced where they matter, access is controlled by role and context, and changes are tracked and auditable.
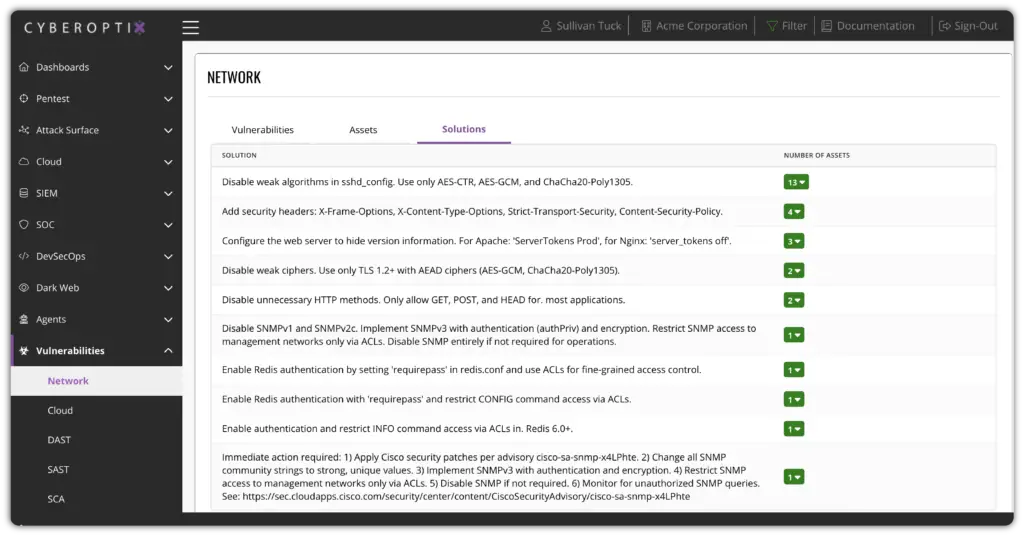
Consistent Protection Across Every Network Layer
Every network layer—perimeter, internal, cloud, and remote access—benefits from the same consistent controls, monitoring, and enforcement, reducing security gaps and improving posture over time.
Security posture improves continuously, not just after audits. Each change to the network is assessed and documented, reducing configuration drift and eliminating blind spots before attackers exploit them.
Built to Protect Your Network Without Slowing It Down
CyberOptix delivers network security as an operational capability, not a collection of point products. These core capabilities work together to continuously monitor for threats, enforce access controls, segment your network, and integrate with the workflows your team already uses.

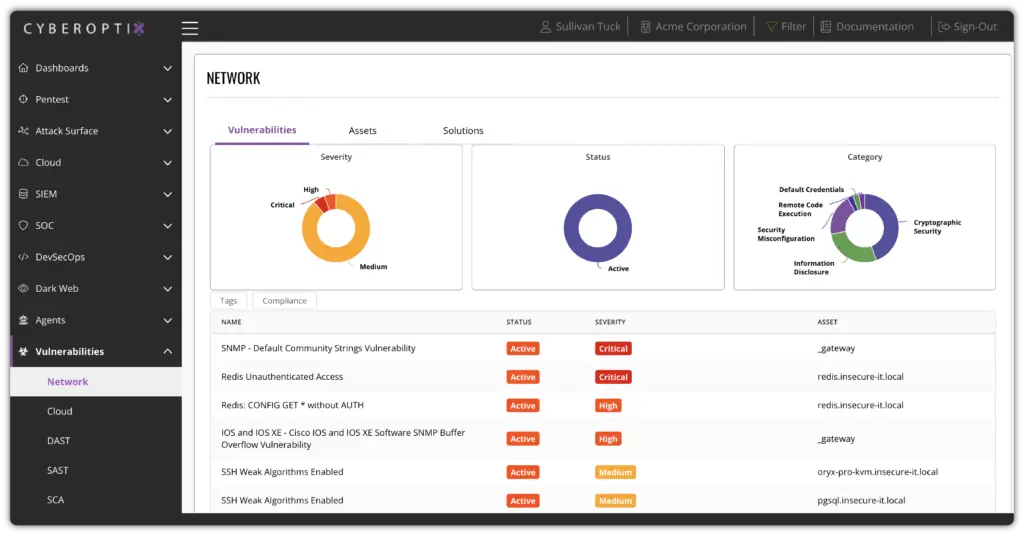
Detect threats the moment they enter your network.
Monitor all network traffic and activity in real time to identify threats, anomalies, and indicators of compromise as they appear. This gives security teams the speed and context to respond before incidents escalate.
Enforce policy and control who accesses what, and when.
Define and enforce granular access policies based on user identity, device posture, and network context. This ensures that only authorized users and systems can reach sensitive resources, reducing your blast radius.
Segment and isolate threats before they can spread.
Divide your network into isolated zones to limit lateral movement and contain threats before they spread. This reduces the impact of breaches and ensures critical systems remain protected even when perimeter defenses are bypassed.
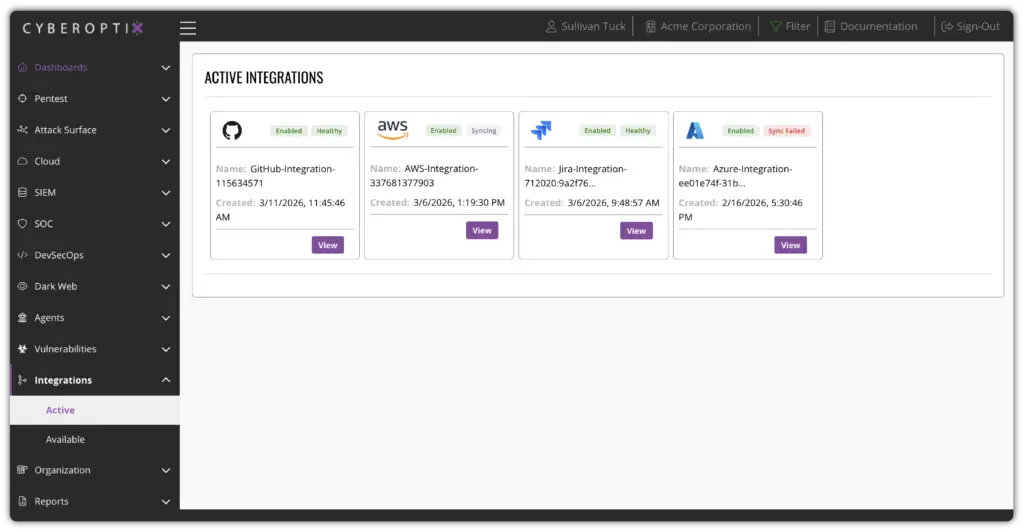
Integrate network security into your existing operations workflows.
Integrate network security alerting, policy management, and incident response directly into your SOC workflows, SIEM, and ticketing systems so your team can act on threats as part of normal operations—without switching tools.
See Network Security in Action
CyberOptix turns network security from a patchwork of disconnected tools into a unified, operational capability. See how continuous monitoring, access control, network segmentation, and workflow integration work together to protect your network without slowing it down.