Empowering SOC teams and penetration testers to detect threats faster, run smarter assessments, and close the gap between findings and remediation.
Most security operations teams are overwhelmed, too many alerts, too little context, and findings that never get resolved. SOC analysts spend more time triaging noise than investigating real threats. Penetration testers generate reports that sit in queues for months.
CyberOptix’s Security Operations solution is built to change that.
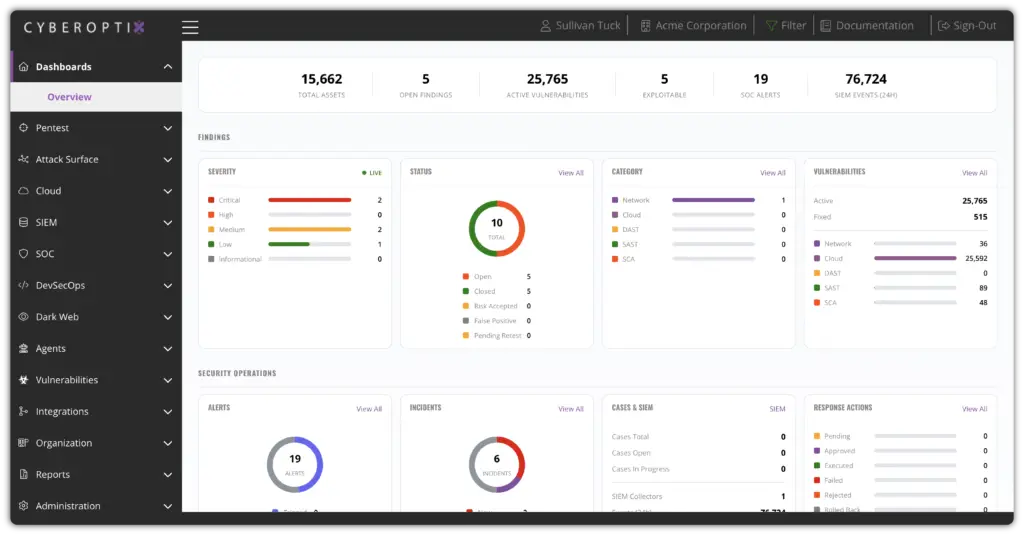
CyberOptix centralizes security event monitoring, alert management, and threat investigation in one unified platform—giving SOC analysts the context they need to respond faster and with more confidence.
Alert volume is tamed through intelligent correlation and risk-based prioritization. Analysts work from a single, structured queue with clear context on each finding, reducing time-to-detect and time-to-respond across every shift.
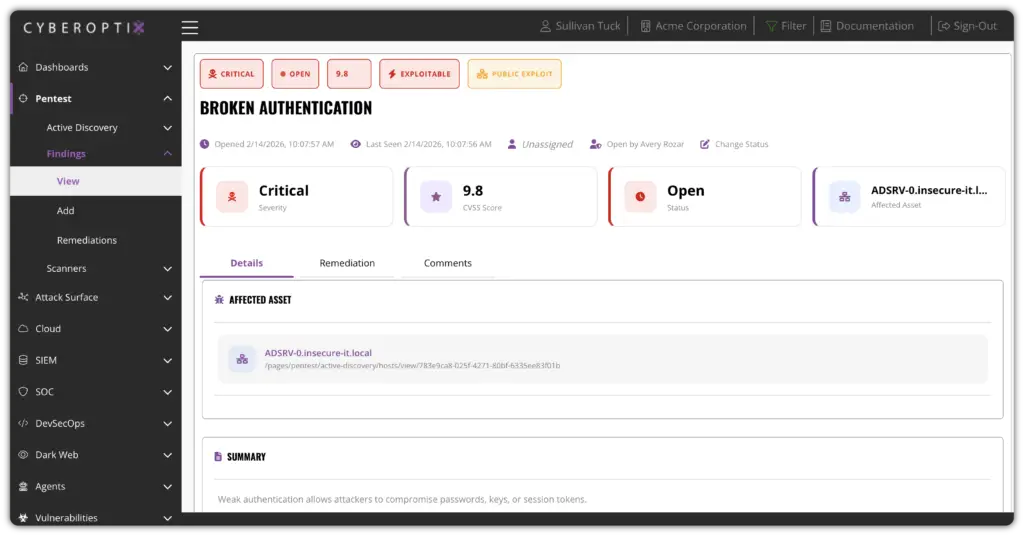
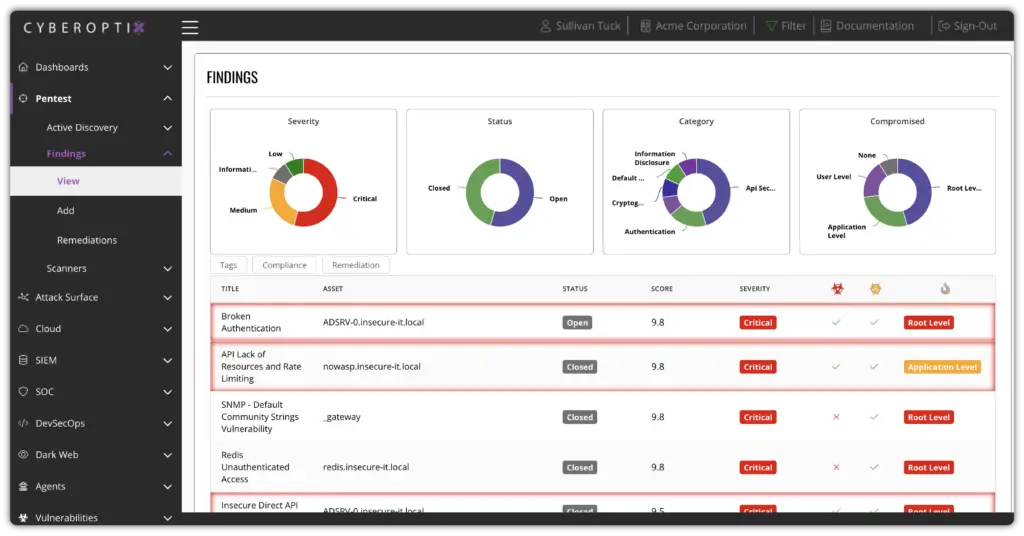
CyberOptix manages the full penetration testing lifecycle—from scoping and scheduling through finding delivery, tracking, and remediation validation. Every engagement generates structured, actionable findings that don’t get lost in a PDF queue.
Pentest findings are connected directly to remediation workflows. Teams can assign, track, and validate fixes in the same platform where findings were reported, closing the loop between testers and the teams responsible for resolving issues.
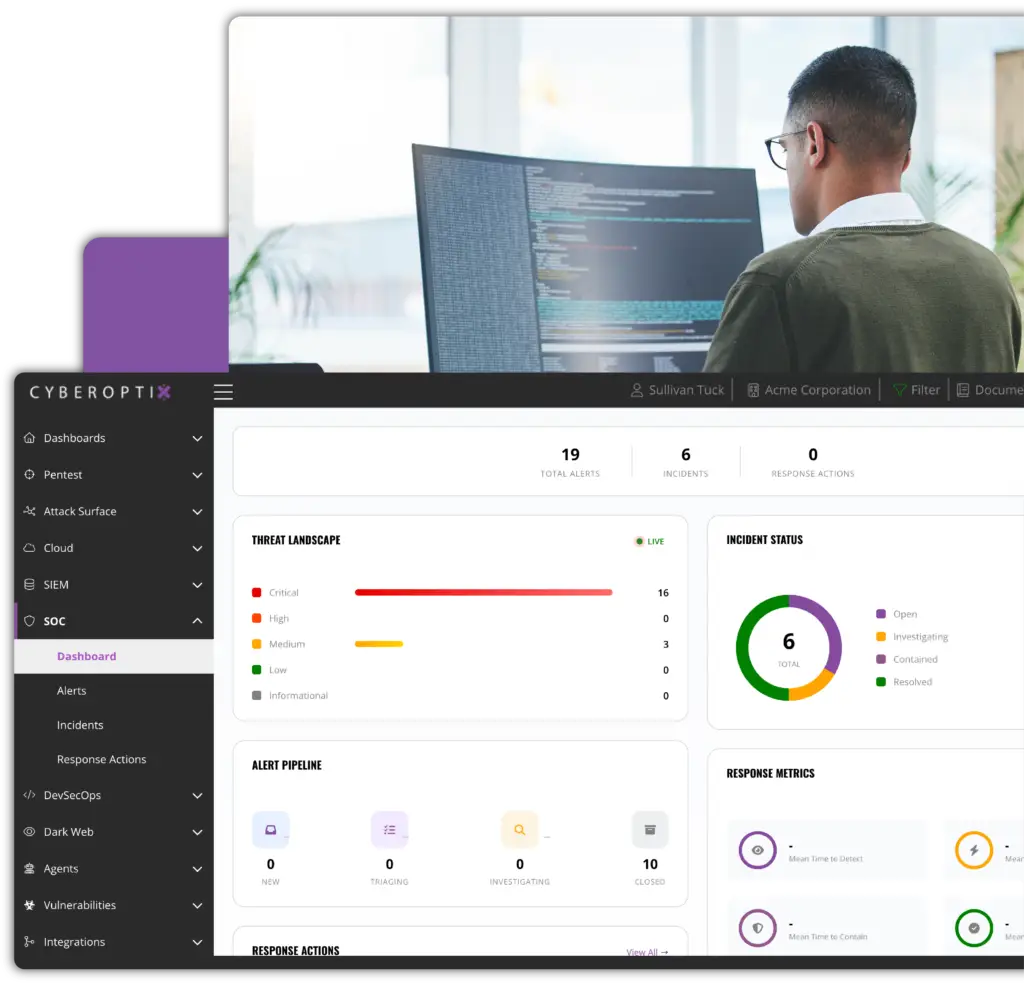
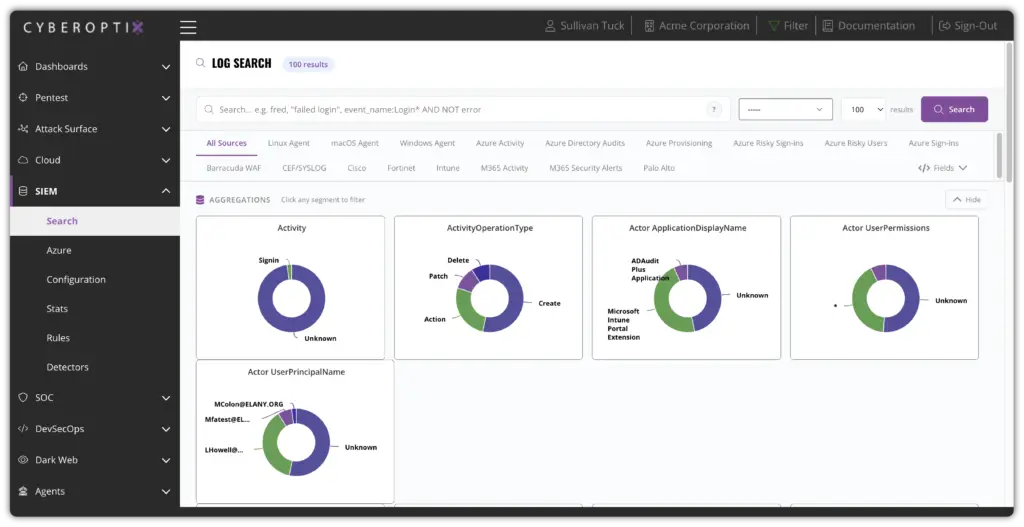
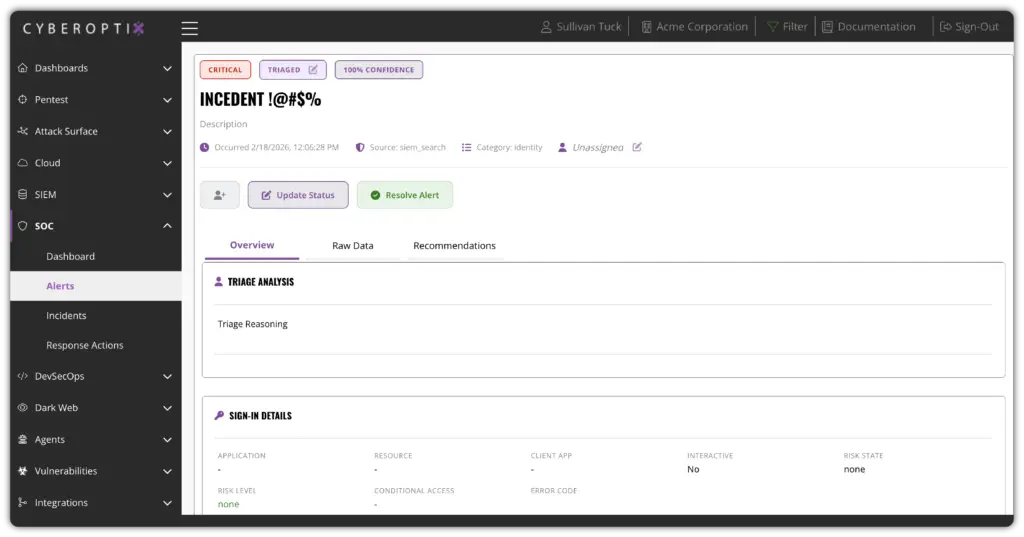
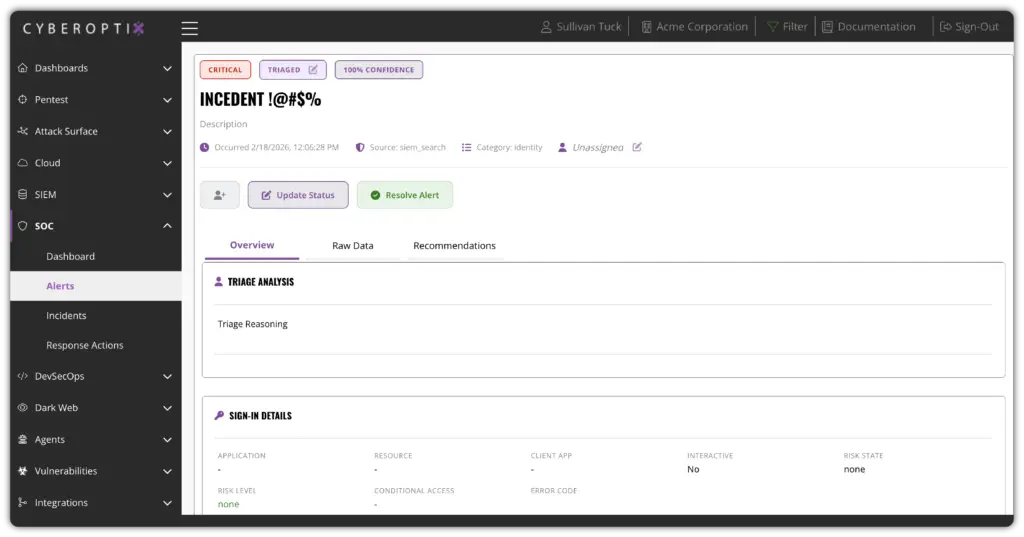
CyberOptix correlates security events across sources to surface the alerts that matter most, complete with enriched context, asset relationships, and risk scoring. SOC analysts spend less time chasing noise and more time on genuine threats.
Instead of manually piecing together signals from disconnected tools, analysts work from a unified incident view with all the context needed to make confident decisions—faster triage, better decisions, reduced dwell time.
CyberOptix gives SOC teams structured workflows that maintain consistent coverage regardless of team size, turnover, or shift changes. Playbooks, runbooks, and escalation paths are built in—not buried in documentation.
Security operations matures over time, not just at audit moments. Coverage stays consistent across shifts, tools stay integrated, and documentation stays current—so new team members ramp faster and institutional knowledge isn’t lost.
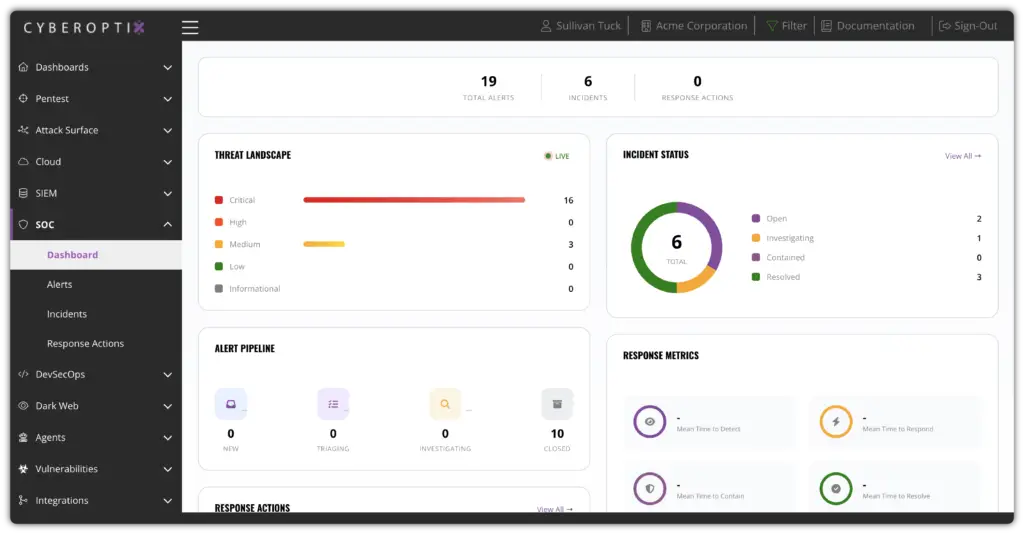
CyberOptix delivers security operations as an ongoing operational capability, not just a collection of point-in-time tools. These core capabilities work together to continuously monitor for threats, manage penetration testing programs, and maintain visibility across your entire security posture.

Continuously monitor your environment for suspicious activity and surface high-priority alerts before threats escalate. CyberOptix aggregates signals across endpoints, networks, and logs to give your SOC team a unified, real-time view of your security posture.
Manage your penetration testing engagements as an ongoing program rather than a one-time event. Schedule assessments, assign testers, track scope, and maintain a full audit trail so your team always knows what has been tested and what findings are still open.
Ingest and correlate threat intelligence feeds to identify indicators of compromise across your environment. Connect external threat data with internal telemetry to detect active campaigns early and prioritize the alerts that matter most to your organization.
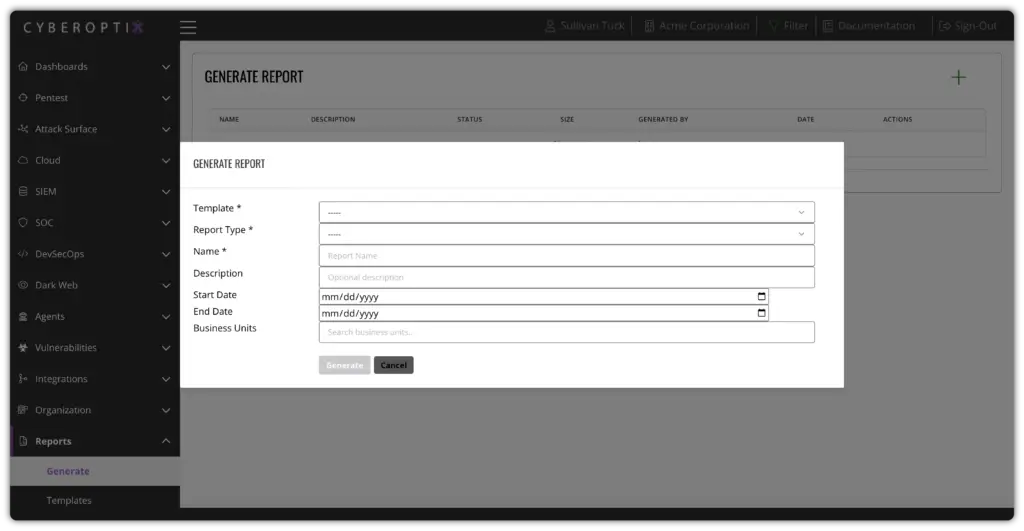
Generate executive and operational reports that reflect your true security status. Track every finding from initial detection through assigned ownership, remediation steps, and final resolution so nothing falls through the cracks.
CyberOptix turns security operations from a reactive, tool-heavy burden into a structured, scalable capability. See how unified SOC monitoring, penetration testing management, and centralized finding workflows work together to reduce real risk and keep your team operating at full effectiveness.