Endpoint Security Solution
Giving security teams complete visibility and control over every endpoint — reducing attacker dwell time and eliminating risk before it can be exploited.
Endpoint Threats Are Evolving Faster Than Your Defenses
Modern endpoint risk doesn’t come from a lack of antivirus software. It comes from security teams lacking real-time visibility into what’s actually running, connecting, and changing across every device. Most teams detect too slowly, respond too narrowly, or lack the context to act on what truly matters.
CyberOptix’s Endpoint Security solution is designed to change that.
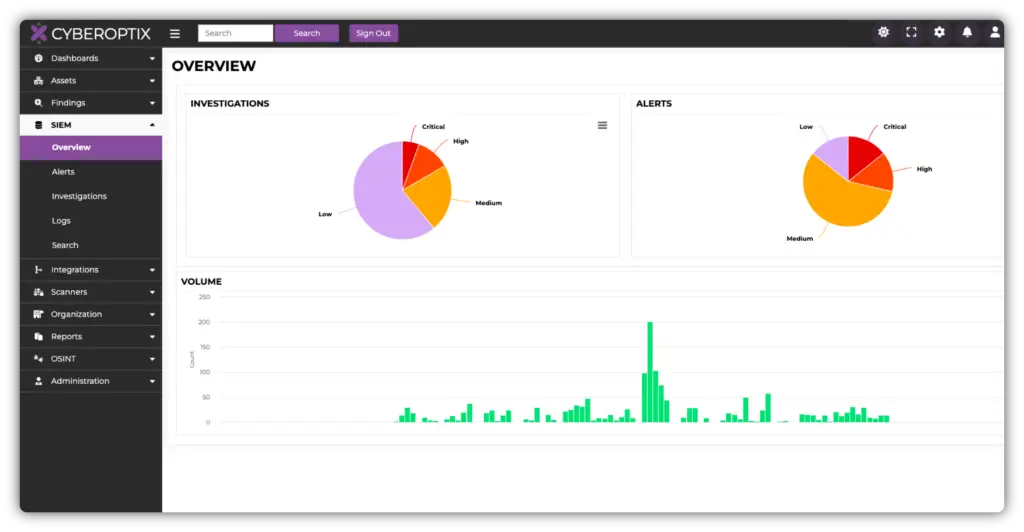
Continuous Endpoint Monitoring and Threat Detection
Endpoint threats don’t wait for scheduled scans. CyberOptix continuously monitors every device in your environment, detecting malicious activity, suspicious behavior, and policy violations in real time as they occur.
Security teams gain a live view of every endpoint’s posture — not a weekly snapshot. Threats are identified as they emerge, reducing dwell time and giving analysts the context to act fast.
Automated Response That Reduces Analyst Workload
When threats are detected, speed of response determines the damage done. CyberOptix automates containment and remediation actions — isolating compromised endpoints, blocking malicious processes, and rolling back unauthorized changes — without waiting for manual intervention.
Security analysts focus on what matters most while routine response actions run automatically. Playbooks enforce consistent, repeatable processes that shrink response time.
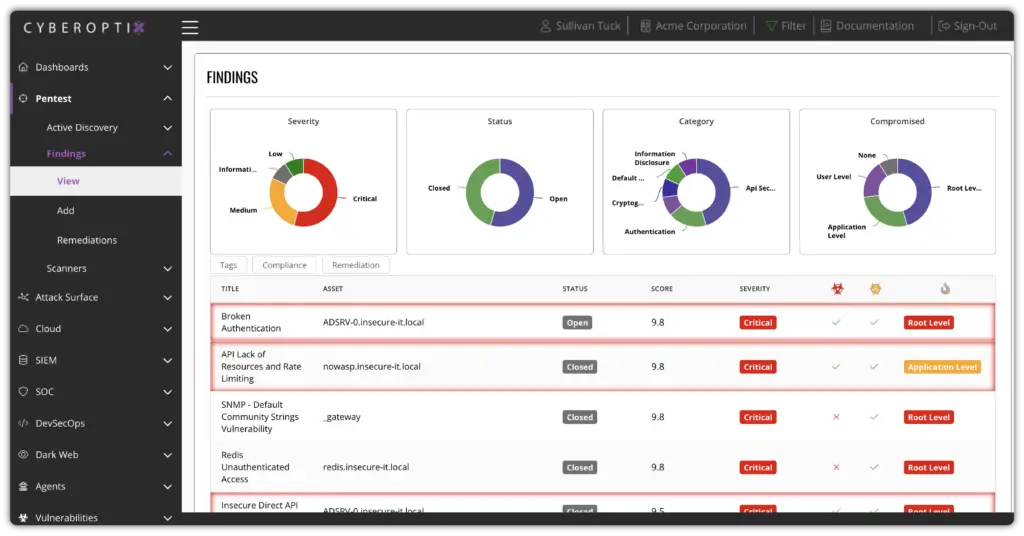
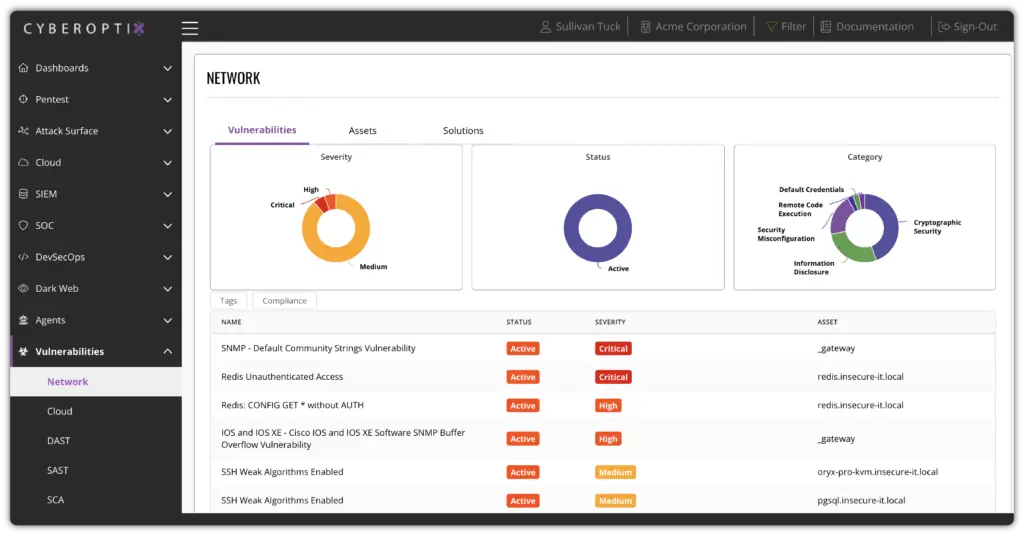
Unified Endpoint Vulnerability Management
Unpatched endpoints are the most common foothold for attackers. CyberOptix continuously inventories software, configurations, and known vulnerabilities across every device, surfacing exploitable weaknesses before adversaries find them.
Risk is prioritized by exploitability and business impact — not just CVSS score — so teams spend time on what truly matters.
Consistent Endpoint Security Across Every Device
Every endpoint — whether managed, unmanaged, remote, or on-premises — benefits from the same consistent monitoring, detection, and response capabilities. Security posture improves continuously, reducing drift and eliminating surprise vulnerabilities at every release cycle.
Built to Eliminate Real Endpoint Risk Without Slowing Operations
CyberOptix delivers endpoint security as an operational capability — not a point-in-time scan. These core capabilities work together to continuously detect threats, prioritize what matters, and help teams respond as part of everyday security operations.

Detect threats with integrated threat intelligence.
Enrich endpoint detections with global threat intelligence feeds, known indicators of compromise (IOCs), and adversary tactics. This enables teams to identify sophisticated attacks — including living-off-the-land techniques — that evade traditional signature-based tools.
Surface and prioritize exploitable endpoint vulnerabilities.
Continuously inventory software versions, configurations, and known CVEs across every device. Risk is prioritized by exploitability and business impact so teams remediate what actually matters — not thousands of low-priority findings.
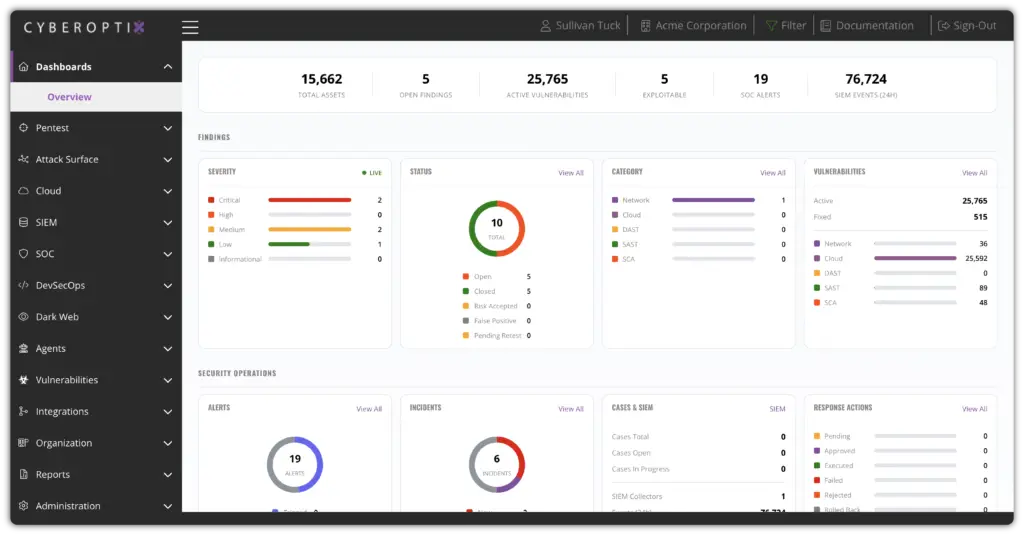
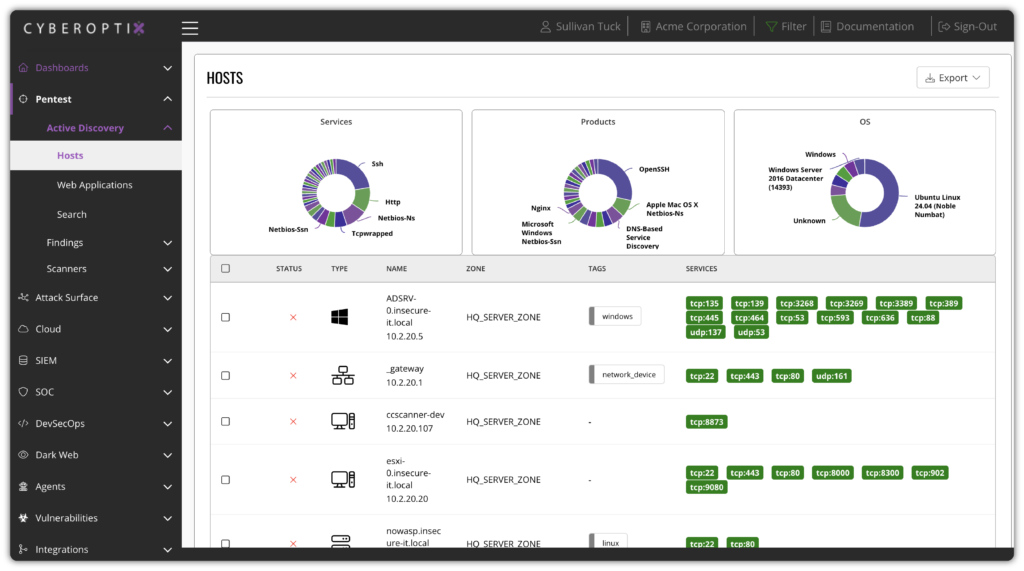
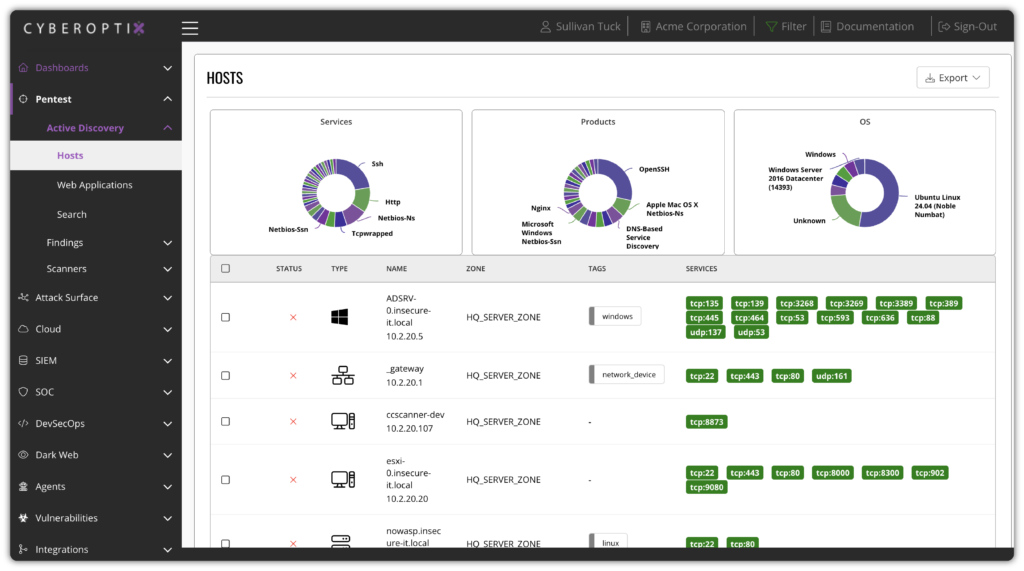
Maintain complete visibility into every device and asset.
Automatically discover and inventory every managed and unmanaged endpoint in your environment. Understanding exactly what devices exist, what software is installed, and what configurations are in place is the foundation of effective endpoint security.
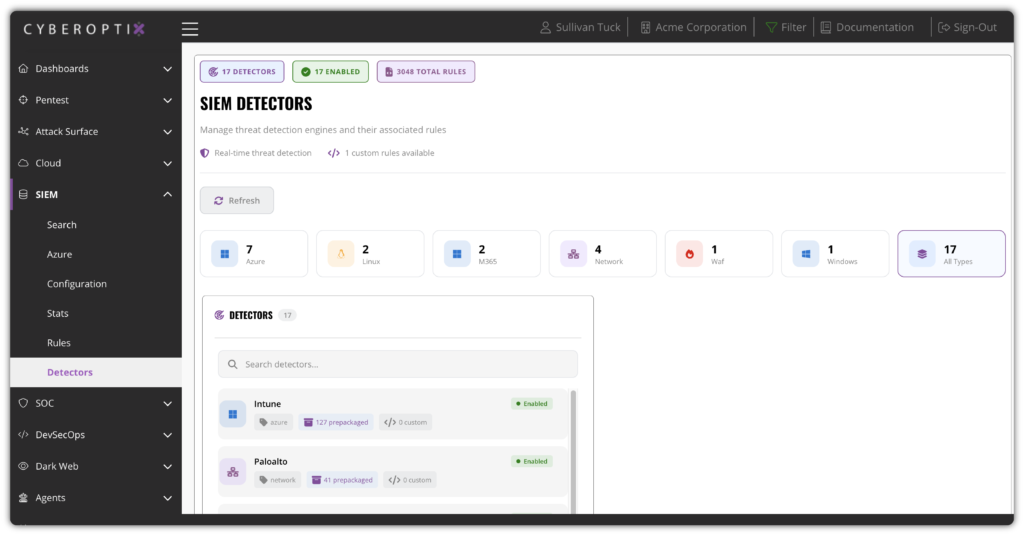
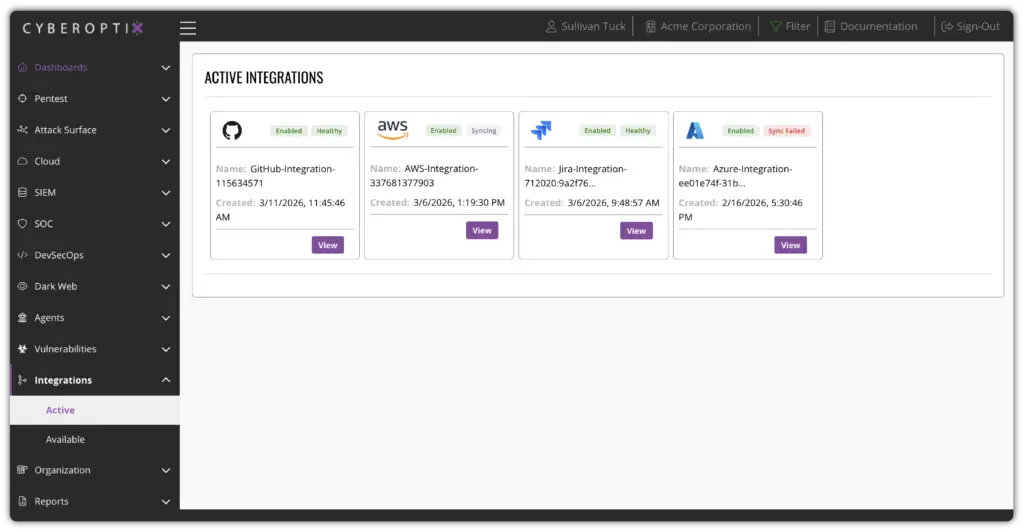
Integrate endpoint data directly into your security stack.
Feed endpoint telemetry directly into SIEM, SOAR, and ticketing platforms so your existing workflows automatically benefit from richer endpoint context. This eliminates tool switching and ensures endpoint data powers your broader detection and response capabilities.
See Endpoint Security in Action
CyberOptix turns endpoint security from a reactive task into a continuous capability built into how your security team operates. See how real-time monitoring, automated response, and centralized visibility work together to reduce real endpoint risk without slowing your organization down.