Threat Intelligence Solution
Empowering security teams to detect, analyze, and respond to emerging threats before they impact your organization.
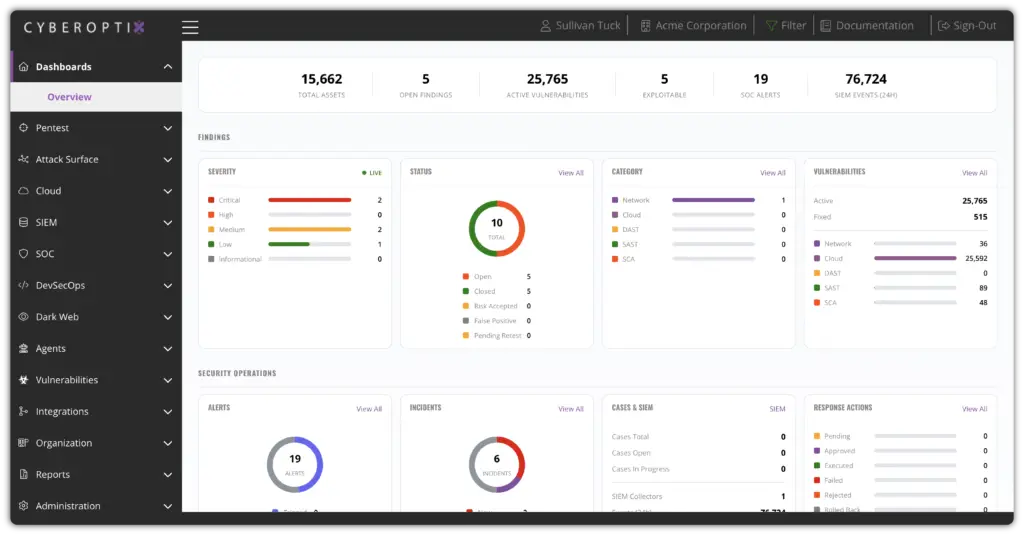
Intelligence That Drives Proactive Defense
Most security teams are reacting to threats rather than anticipating them. Alerts pile up without context, threat feeds deliver noise instead of signal, and analysts spend hours on research that should take minutes.
CyberOptix’s Threat Intelligence solution is designed to change that.
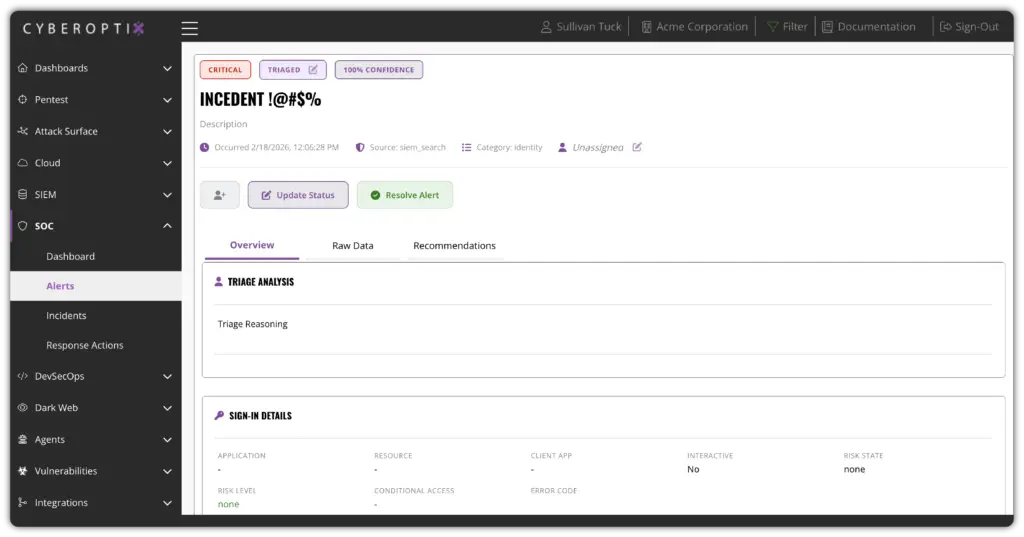
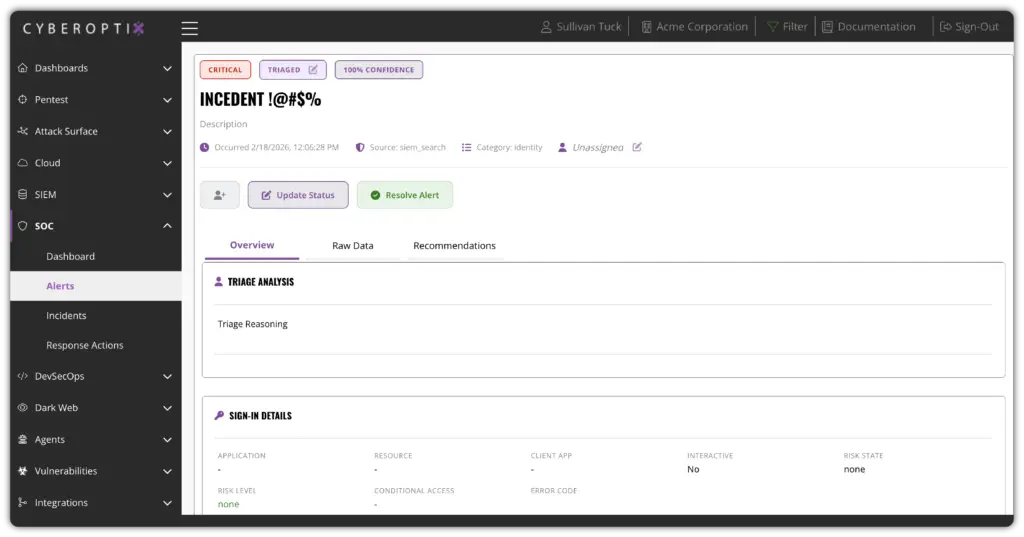
Real-Time Threat Detection and Monitoring
Threat intelligence is continuously collected, correlated, and delivered in real time—giving your team visibility into active adversaries, emerging attack patterns, and indicators of compromise before they become incidents.
Threat monitoring becomes an always-on capability rather than a periodic investigation. Risks are surfaced in context, validated against your environment, and acted upon before they reach critical stages.
Contextual Threat Enrichment and Analysis
Every threat indicator is automatically enriched with adversary context, campaign history, and relevance to your specific environment—turning raw data into intelligence your team can immediately act on.
Instead of leaving analysts to manually research IOCs, CyberOptix delivers enriched, contextualized intelligence directly within the platform, reducing investigation time and improving analyst confidence.
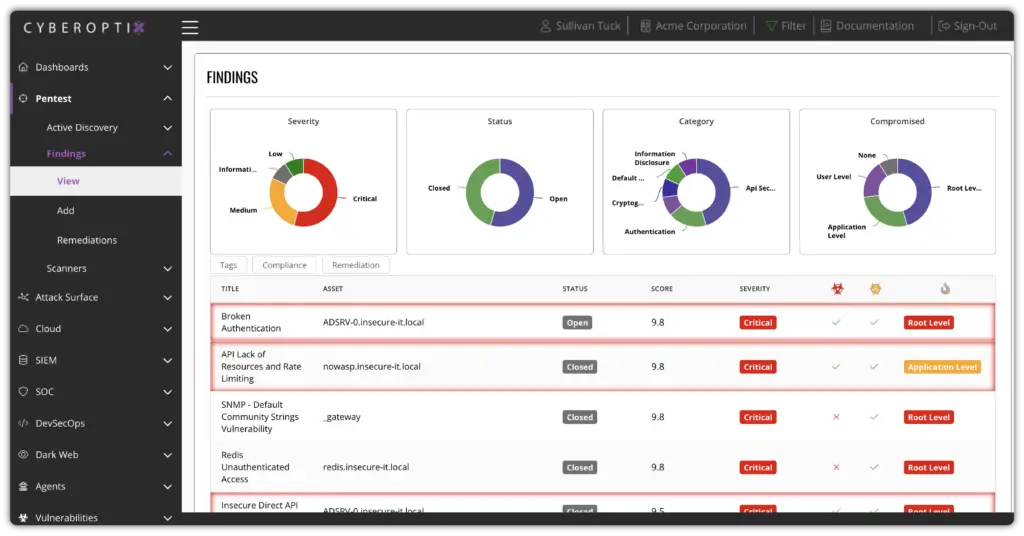
Prioritized, Actionable Threat Feeds
Threat intelligence is filtered, scored, and prioritized based on your attack surface—so analysts focus on what poses real risk rather than chasing low-relevance alerts.
Instead of drowning in unfiltered feeds, teams receive curated, high-fidelity intelligence mapped to your environment. The right threats reach the right people, accelerating response and reducing mean time to detect.
Continuous Threat Coverage Across Your Organization
Every team—SOC, red team, and leadership—benefits from the same consistent threat picture, reducing blind spots and improving organizational security maturity over time.
Threat visibility improves continuously, not just during incidents. Every team benefits from the same level of intelligence, analysis, and context, reducing gaps and eliminating surprise exposures before they become breaches.
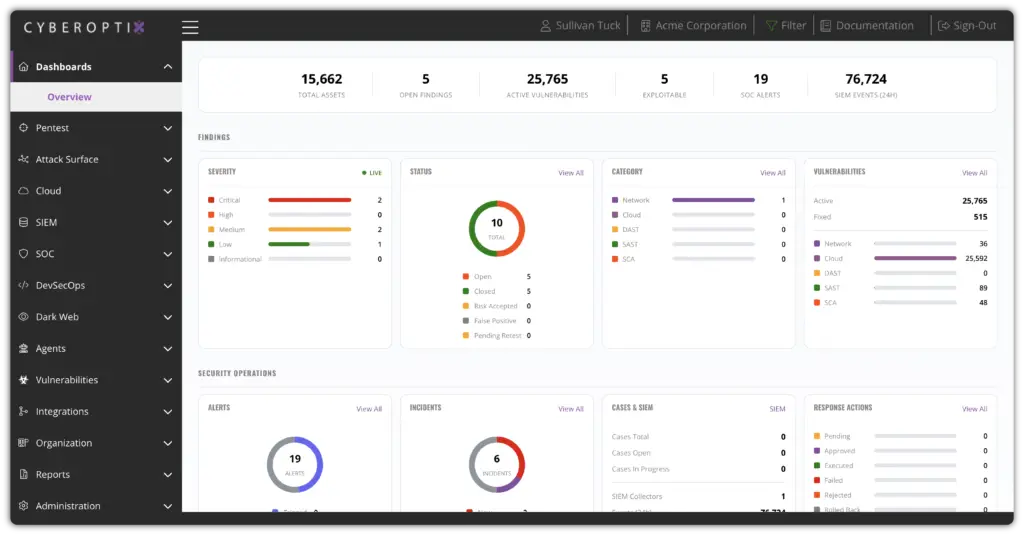
Built to Turn Intelligence Into Decisive Action
CyberOptix delivers threat intelligence as an operational capability, not a feed subscription. These core capabilities work together to continuously collect, enrich, and deliver actionable intelligence that helps your team stay ahead of adversaries.

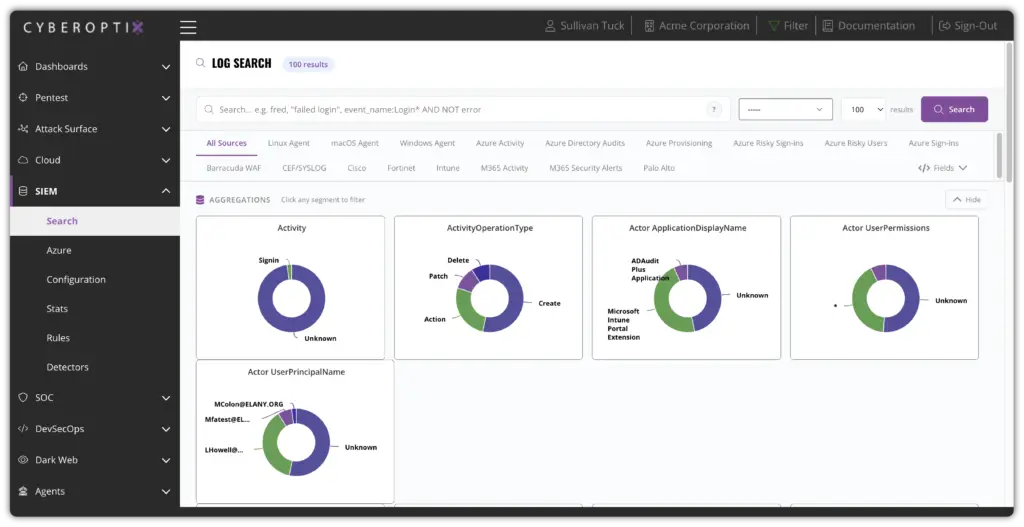
Monitor open source and dark web channels for early threat signals.
Continuously monitor dark web forums, paste sites, threat actor communities, and open-source intelligence sources for indicators relevant to your organization. This enables teams to identify emerging threats before they materialize into incidents.
Track adversaries, campaigns, and TTPs across your threat landscape.
Track known and emerging threat actors, their tools, techniques, and procedures (TTPs), and active campaigns targeting your industry. This provides the strategic context needed to prioritize defenses and anticipate attacker behavior.
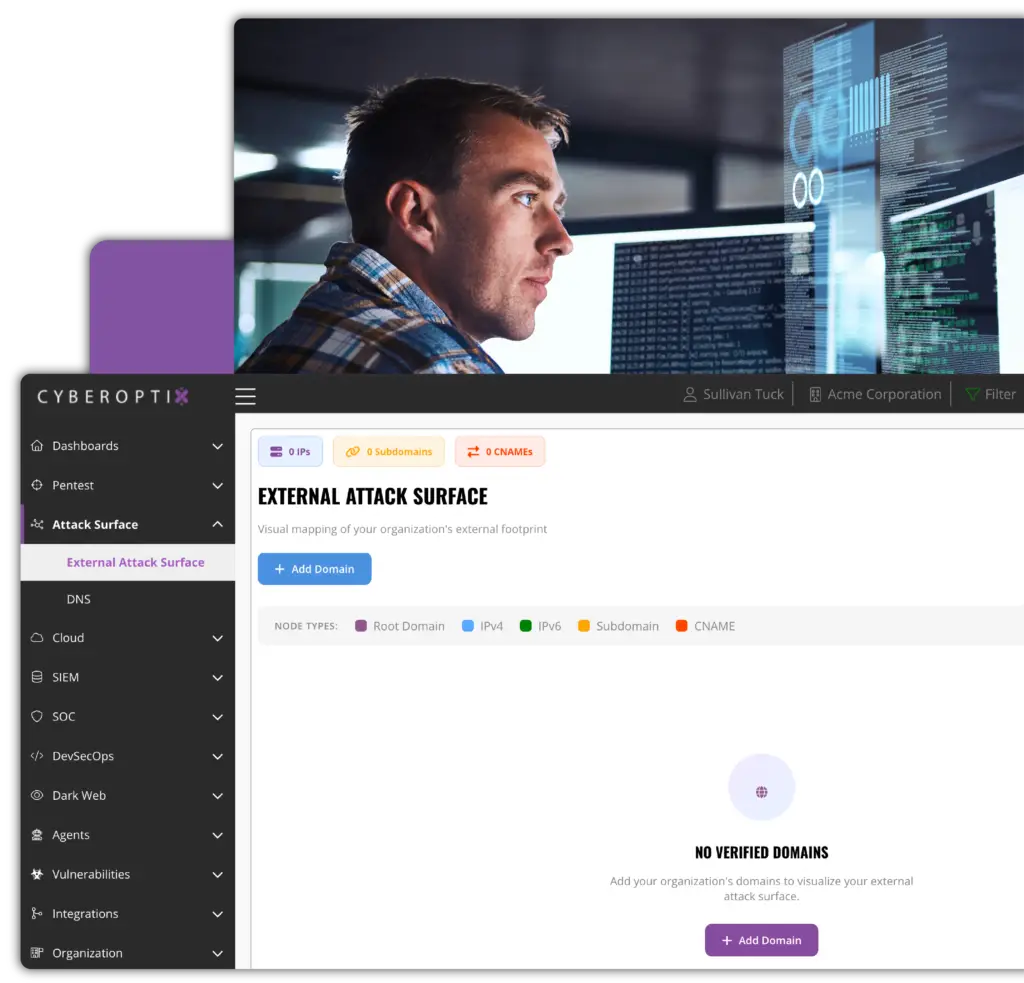
Centralize and manage indicators of compromise across your environment.
Aggregate, deduplicate, and manage indicators of compromise—including IPs, domains, hashes, and URLs—from multiple sources in a single, searchable repository. This reduces analyst workload and improves detection consistency across your security tools.
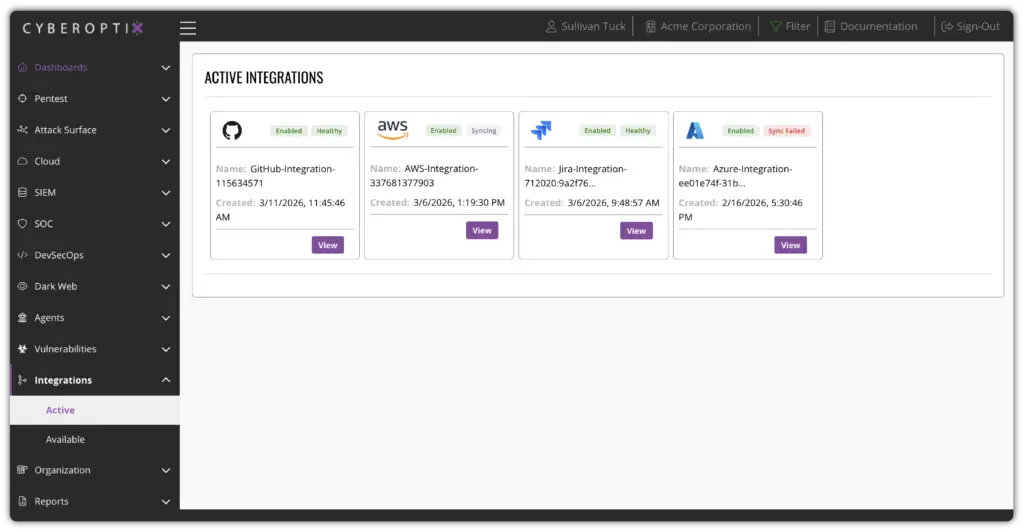
Connect threat intelligence to your existing SIEM, SOAR, and security stack.
Push enriched threat intelligence directly into your SIEM, SOAR, ticketing systems, and endpoint tools via native integrations and APIs. This keeps your entire security stack informed without manual data transfers or workflow gaps.
See Threat Intelligence in Action
CyberOptix turns threat intelligence from a passive feed into an active defense capability. See how continuous monitoring, automated enrichment, and centralized intelligence management work together to detect and respond to real threats before they impact your organization.